Thomas Konrad
Software Security 101: Secure Coding Basics
#1about 15 minutes
Understanding core software security principles and terminology
Key concepts like the CIA triad, technical debt, and design principles provide a shared language for discussing security.
#2about 19 minutes
Evaluating programming languages for security features
Criteria like memory safety, type strictness, and sandbox support help in selecting a language that mitigates entire classes of vulnerabilities by design.
#3about 13 minutes
Implementing secure input and output handling
Proper input validation, canonicalization, sanitization, and context-sensitive output encoding are crucial for preventing injection attacks.
#4about 5 minutes
Avoiding pitfalls in low-level languages and enforcing access control
Low-level languages require manual bounds checking to prevent buffer overflows, while complete mediation ensures access control is checked on every request.
#5about 8 minutes
Applying cryptography and managing user sessions securely
Use standard, well-vetted cryptographic libraries and follow best practices for session management to protect data and user identity.
#6about 9 minutes
Handling concurrency to prevent data integrity issues
Race conditions can lead to data integrity problems, which can be mitigated using techniques like entity versioning or resource locking.
#7about 12 minutes
Understanding common web and API vulnerability classes
Familiarity with lists like the OWASP Top 10 and CWE Top 25 helps in creating targeted protection strategies for specific vulnerabilities like cross-site scripting.
#8about 5 minutes
Managing third-party software dependencies for security
Automating dependency checks for known vulnerabilities is essential because third-party libraries often constitute the majority of an application's code.
#9about 7 minutes
Integrating security into the software development lifecycle
Using a maturity model like OWASP SAM helps shift security left by incorporating activities like threat modeling early in the design phase.
#10about 19 minutes
Key takeaways and resources for continuous security learning
Cultivate a culture of continuous learning by using resources like OWASP Juice Shop and focusing on understanding the entire technology stack.
Related jobs
Jobs that call for the skills explored in this talk.
Matching moments

02:26 MIN
Why developers make basic cybersecurity mistakes
Don't Be A Naive Developer: How To Avoid Basic Cybersecurity Mistakes
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
06:06 MIN
Foundational practices for writing secure software code
Security Pitfalls for Software Engineers
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

04:38 MIN
Hands-on security training for developers
How GitHub secures open source
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
02:23 MIN
Key strategies for building a secure code culture
Secure Code Superstars: Empowering Developers and Surpassing Security Challenges Together
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

03:34 MIN
Addressing the security education gap for developers
Climate vs. Weather: How Do We Sustainably Make Software More Secure?
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

05:26 MIN
The difference between secure coding and secure development
Maturity assessment for technicians or how I learned to love OWASP SAMM
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
04:09 MIN
Introduction to developer-first security and CTFs
Capture the Flag 101
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
06:45 MIN
How to effectively train your security champions
Building Security Champions
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
Featured Partners
Related Videos
 27:32
27:32Security Pitfalls for Software Engineers
Jasmin Azemović
 58:19
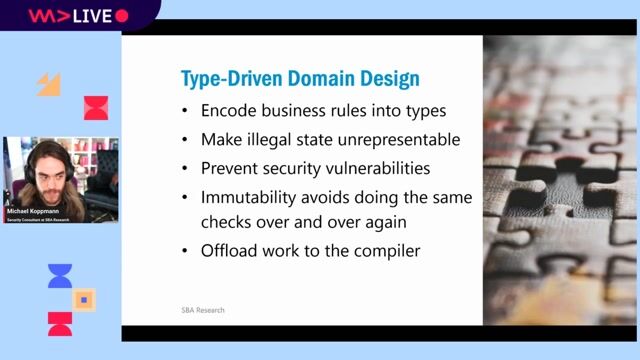
58:19Typed Security: Preventing Vulnerabilities By Design
Michael Koppmann
 29:47
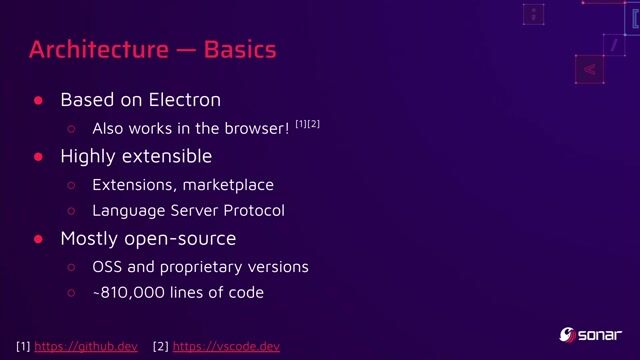
29:47You click, you lose: a practical look at VSCode's security
Thomas Chauchefoin & Paul Gerste
 48:02
48:02Building Security Champions
Tanya Janca
 1:41:05
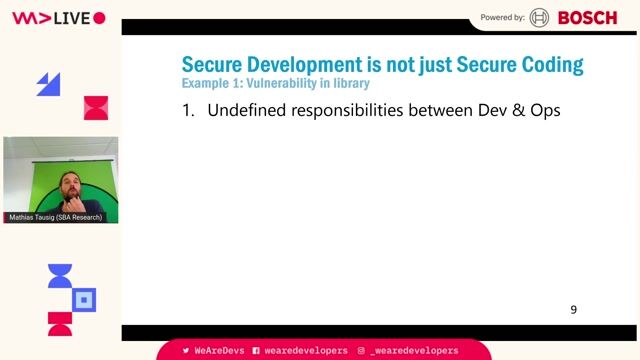
1:41:05Maturity assessment for technicians or how I learned to love OWASP SAMM
Mathias Tausig
 29:34
29:34You can’t hack what you can’t see
Reto Kaeser
 36:39
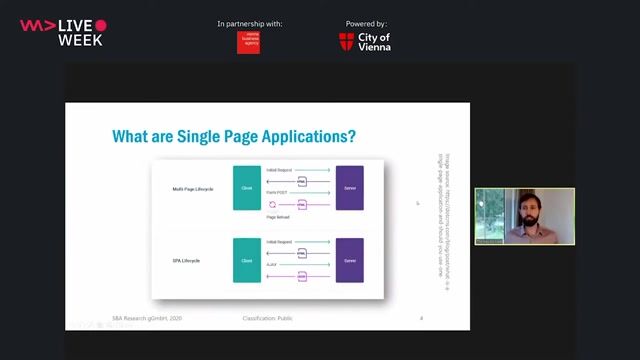
36:39A Primer in Single Page Application Security (Angular, React, Vue.js)
Thomas Konrad
 33:29
33:29Programming secure C#/.NET Applications: Dos & Don'ts
Sebastian Leuer
Related Articles
View all articles

.png?w=240&auto=compress,format)

From learning to earning
Jobs that call for the skills explored in this talk.

Speech Processing Solutions
Vienna, Austria
Intermediate
CSS
HTML
JavaScript
TypeScript

Vesterling Consulting GmbH
€70-90K
Software Architecture

Hochschule Luzern

NTT DATA Deutschland GmbH
Remote
Node.js
Continuous Integration

NTT DATA Deutschland GmbH
Remote
Node.js
Continuous Integration

Fraunhofer-Gesellschaft

Excellence AG
Kotlin
Kubernetes
Apache Kafka
Microservices
Continuous Delivery
+1

M Plan Modulare Planungs- und Konstruktionstechnik GmbH
