Reto Kaeser
You can’t hack what you can’t see
#1about 3 minutes
The cultural shift from DevOps to DevSecOps
DevOps succeeded by fostering a culture of shared responsibility, and now security must be integrated to break down the final silo.
#2about 8 minutes
Integrating security into requirements and design phases
Proactively address security by defining abuse cases during requirements and classifying or anonymizing data during the design phase.
#3about 5 minutes
Hardening the CI/CD pipeline with automated security tools
Shift security left by integrating automated vulnerability management for dependencies and continuous penetration testing into the CI/CD process.
#4about 3 minutes
Why traditional firewalls fail against internal east-west traffic
Most network traffic occurs internally between services (east-west), bypassing perimeter firewalls and exposing a soft interior to application-level attacks.
#5about 3 minutes
Moving from perimeter defense to workload microsegmentation
Protect against internal threats by decoupling security from the network and applying logical firewalls directly to each workload through microsegmentation.
#6about 4 minutes
Applying Zero Trust principles with security as code
Implement a Zero Trust model by having developers define workload communication intentions as code, which automatically generates and enforces security policies.
#7about 2 minutes
The benefits of a modern workload-centric security architecture
Adopting a Zero Trust, workload-centric model provides benefits like increased agility, complete application-level visibility, automated compliance, and real-time forensics.
#8about 1 minute
A developer's responsibility to build secure software
Developers must take ownership of security by adopting a paranoid mindset to build more resilient software in an increasingly dangerous cloud environment.
Related jobs
Jobs that call for the skills explored in this talk.
Matching moments

05:49 MIN
Cybersecurity is a foundational necessity not a passing trend
Decoding Trends: Strategies for Success in the Evolving Digital Domain
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
03:08 MIN
Shifting security left with collaborative threat modeling
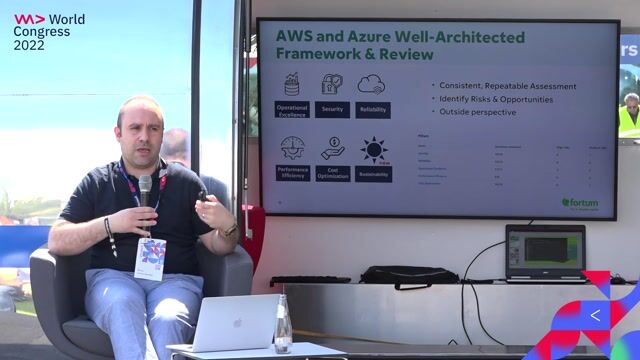
We adopted DevOps and are Cloud-native, Now What?
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

04:48 MIN
The expanding role of developers in security
Vulnerable VS Code extensions are now at your front door
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
03:50 MIN
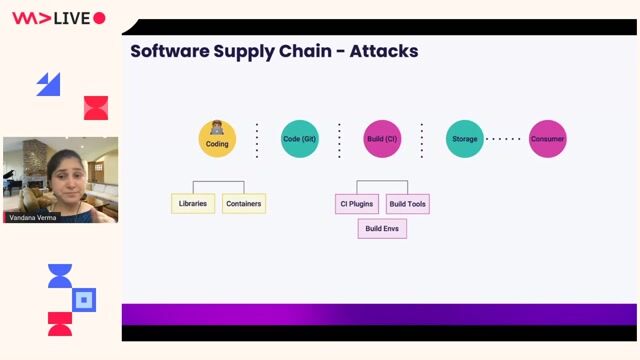
Common attack vectors and the zero trust principle
Walking into the era of Supply Chain Risks
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

04:29 MIN
The modern DevSecOps approach to application security
Maturity assessment for technicians or how I learned to love OWASP SAMM
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
04:00 MIN
The expanding security responsibilities of developers
Vue3 practical development
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

02:26 MIN
Why developers make basic cybersecurity mistakes
Don't Be A Naive Developer: How To Avoid Basic Cybersecurity Mistakes
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
02:28 MIN
Key takeaways on IDE and developer tool security
You click, you lose: a practical look at VSCode's security
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
Featured Partners
Related Videos
 33:20
33:20DevSecOps: Security in DevOps
Aarno Aukia
 51:41
51:41Climate vs. Weather: How Do We Sustainably Make Software More Secure?
Panel Discussion
 45:19
45:19Security Challenges of Breaking A Monolith
Reinhard Kugler
 44:30
44:30Securing Your Web Application Pipeline From Intruders
Milecia McGregor
 43:56
43:56Getting under the skin: The Social Engineering techniques
Mauro Verderosa
 37:32
37:32Cyber Security: Small, and Large!
Martin Schmiedecker
 1:41:05
1:41:05Maturity assessment for technicians or how I learned to love OWASP SAMM
Mathias Tausig
 58:19
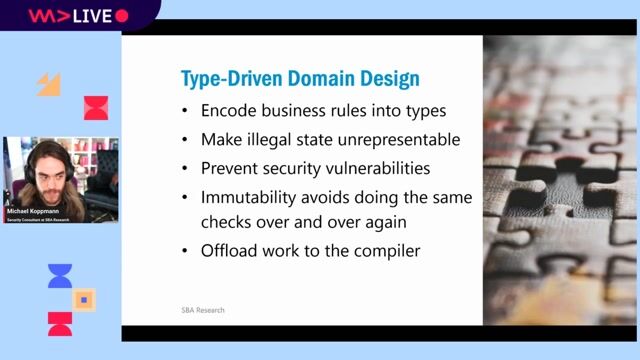
58:19Typed Security: Preventing Vulnerabilities By Design
Michael Koppmann
Related Articles
View all articles

.png?w=240&auto=compress,format)

From learning to earning
Jobs that call for the skills explored in this talk.


NTT DATA Deutschland GmbH
Remote
Node.js
Continuous Integration

NTT DATA Deutschland GmbH
Remote
Node.js
Continuous Integration


cyberunity AG
DevOps
Terraform
Network Security



RDT INGENIEROS

Akkodis Germany GmbH