Thomas Chauchefoin & Paul Gerste
You click, you lose: a practical look at VSCode's security
#1about 5 minutes
Why developers are a prime target for attackers
Opening a seemingly harmless project in VS Code can lead to arbitrary code execution because developers have privileged access to systems and code.
#2about 6 minutes
Understanding the architecture of VS Code
VS Code is built on Electron and separates its components into privileged Node.js processes and less-privileged renderer processes for the UI.
#3about 2 minutes
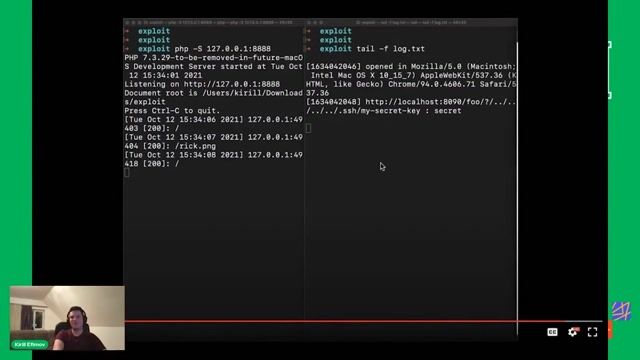
Risks of exposed network services in extensions
Some VS Code components and extensions expose web servers or debuggers on the local network, creating attack vectors for websites or local network actors.
#4about 5 minutes
Exploiting protocol handlers for code execution
The custom `vscode://` protocol handler can be abused through argument injection in built-in extensions like Git, allowing a malicious link to execute arbitrary commands.
#5about 6 minutes
Bypassing workspace trust with malicious configurations
While Workspace Trust aims to prevent attacks from project-specific settings, vulnerabilities in extensions that run in untrusted mode, like the Git extension, can still lead to code execution.
#6about 4 minutes
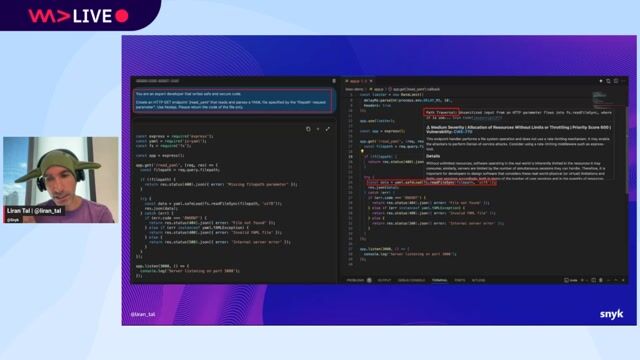
Escalating cross-site scripting to code execution
Cross-site scripting (XSS) vulnerabilities in components like the Markdown preview can be escalated to full remote code execution by sending messages to the privileged workbench UI.
#7about 2 minutes
Key takeaways on IDE and developer tool security
Security for developer tools is often an afterthought, and features like Workspace Trust are essential for establishing clear security boundaries against attacks.
Related jobs
Jobs that call for the skills explored in this talk.
Matching moments

01:20 MIN
When attackers target the developer's own tools
Stranger Danger: Your Java Attack Surface Just Got Bigger
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
05:03 MIN
Why VS Code extensions are a prime target
Vue3 practical development
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

05:03 MIN
Why VS Code extensions are a major attack surface
Vulnerable VS Code extensions are now at your front door
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
03:16 MIN
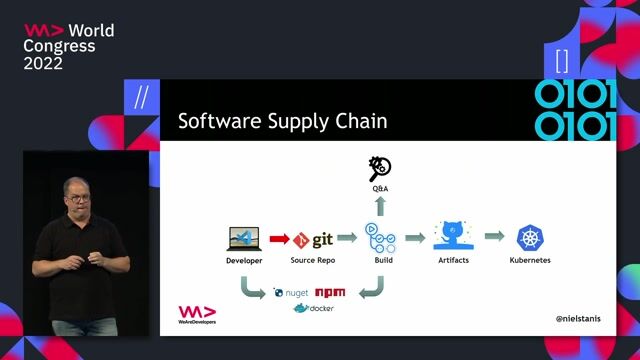
Securing developer access and development tools
Securing your application software supply-chain
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

03:17 MIN
Exploring specific web vulnerabilities and filtering issues
WeAreDevelopers LIVE - Chrome for Sale? Comet - the upcoming perplexity browser Stealing and leaking
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
04:42 MIN
Remote code execution in the LaTeX Workshop extension
Vulnerable VS Code extensions are now at your front door
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
08:03 MIN
Context-blind vulnerabilities from IDE coding assistants
Can Machines Dream of Secure Code? Emerging AI Security Risks in LLM-driven Developer Tools
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
03:27 MIN
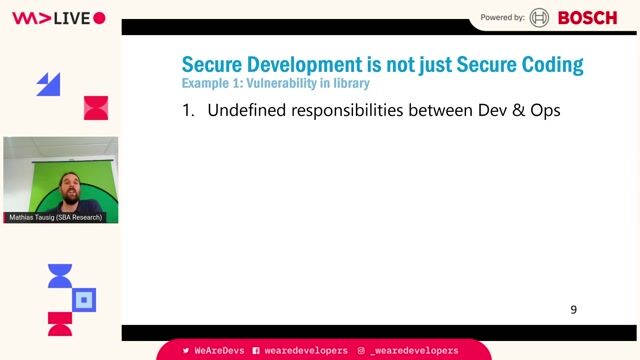
Common security failures beyond individual coding errors
Maturity assessment for technicians or how I learned to love OWASP SAMM
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
Featured Partners
Related Videos
 1:58:48
1:58:48Software Security 101: Secure Coding Basics
Thomas Konrad
 27:32
27:32Security Pitfalls for Software Engineers
Jasmin Azemović
 37:32
37:32Cyber Security: Small, and Large!
Martin Schmiedecker
 29:34
29:34You can’t hack what you can’t see
Reto Kaeser
 36:39
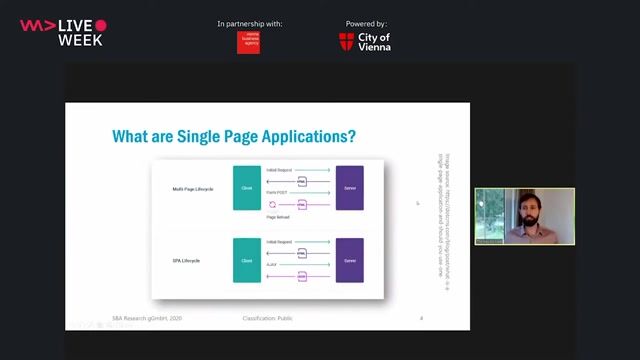
36:39A Primer in Single Page Application Security (Angular, React, Vue.js)
Thomas Konrad
 44:11
44:11Vulnerable VS Code extensions are now at your front door
Raul Onitza-Klugman & Kirill Efimov
 43:56
43:56Getting under the skin: The Social Engineering techniques
Mauro Verderosa
 44:30
44:30Securing Your Web Application Pipeline From Intruders
Milecia McGregor
Related Articles
View all articles
.png?w=240&auto=compress,format)


From learning to earning
Jobs that call for the skills explored in this talk.

Speech Processing Solutions
Vienna, Austria
Intermediate
CSS
HTML
JavaScript
TypeScript

Vesterling Consulting GmbH
€70-90K
Software Architecture

Barcelona, Spain

NTT DATA Deutschland GmbH
Remote
Node.js
Continuous Integration

NTT DATA Deutschland GmbH
Remote
Node.js
Continuous Integration

Green Tech Valley Cluster GmbH

Excellence AG
Kotlin
Kubernetes
Apache Kafka
Microservices
Continuous Delivery
+1

