Jasmin Azemović
Security Pitfalls for Software Engineers
#1about 4 minutes
The high cost and consequences of security breaches
Major companies like Uber and Microsoft have suffered massive data breaches, costing millions and highlighting the severe financial and reputational risks of poor security.
#2about 6 minutes
Foundational practices for writing secure software code
Writing secure code starts with fundamental practices like proper input validation, applying threat modeling methodologies like STRIDE, and adhering to the principle of least privilege.
#3about 5 minutes
Mitigating supply chain attacks with DevSecOps practices
Vulnerabilities in third-party libraries, like the SolarWinds and Log4j incidents, necessitate a DevSecOps approach to integrate security checks throughout the software development lifecycle.
#4about 2 minutes
Essential security measures for protecting public APIs
Publicly exposed APIs must be protected using strong authentication, TLS/SSL encryption for data in transit, and defenses against common attack vectors.
#5about 5 minutes
Protecting data with database encryption and temporal tables
Encrypting sensitive data at the database level protects it even if breached, while temporal tables provide a complete audit trail for forensic analysis.
#6about 2 minutes
Implementing a robust penetration testing strategy
Regular penetration testing, distinct from QA, should be a standard practice using methodologies like black-box or white-box testing and frameworks like the OWASP Top 10.
#7about 1 minute
Maintaining security by separating work and personal devices
Avoid using company-issued laptops for personal or freelance projects to prevent legal liabilities and security compromises between environments.
#8about 3 minutes
Q&A on vulnerable libraries and team security responsibility
The session concludes with answers to audience questions about tracking open-source vulnerabilities, choosing a pen test environment, and clarifying security roles within an agile team.
Related jobs
Jobs that call for the skills explored in this talk.
Matching moments

05:49 MIN
Cybersecurity is a foundational necessity not a passing trend
Decoding Trends: Strategies for Success in the Evolving Digital Domain
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

02:26 MIN
Why developers make basic cybersecurity mistakes
Don't Be A Naive Developer: How To Avoid Basic Cybersecurity Mistakes
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

04:25 MIN
Balancing developer and stakeholder security priorities
What The Hack is Web App Sec?
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

05:31 MIN
From vulnerability researcher to automated security founder
The transformative impact of GenAI for software development and its implications for cybersecurity
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
03:27 MIN
Common security failures beyond individual coding errors
Maturity assessment for technicians or how I learned to love OWASP SAMM
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
02:23 MIN
Key strategies for building a secure code culture
Secure Code Superstars: Empowering Developers and Surpassing Security Challenges Together
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

03:35 MIN
Exploring the need for regulation in software development
Climate vs. Weather: How Do We Sustainably Make Software More Secure?
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
03:08 MIN
Shifting security left with collaborative threat modeling
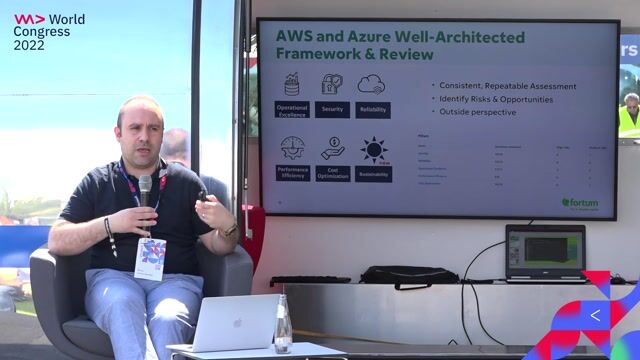
We adopted DevOps and are Cloud-native, Now What?
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
Featured Partners
Related Videos
 22:09
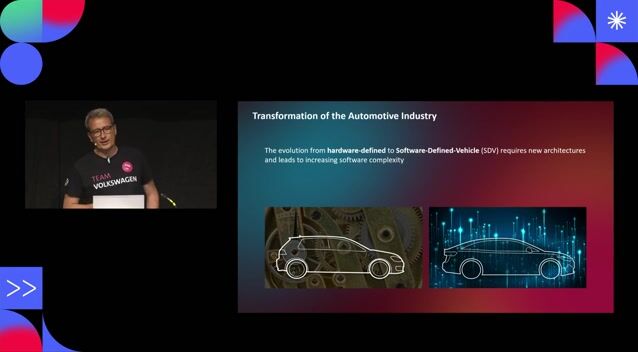
22:09Cybersecurity for Software Defined Vehicles
Henning Harbs
 1:58:48
1:58:48Software Security 101: Secure Coding Basics
Thomas Konrad
 29:47
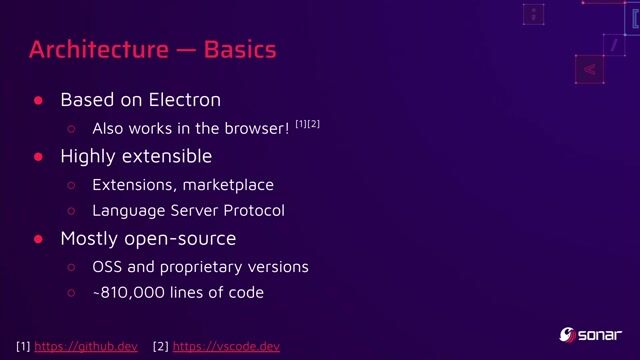
29:47You click, you lose: a practical look at VSCode's security
Thomas Chauchefoin & Paul Gerste
 29:34
29:34You can’t hack what you can’t see
Reto Kaeser
 51:41
51:41Climate vs. Weather: How Do We Sustainably Make Software More Secure?
Panel Discussion
 37:32
37:32Cyber Security: Small, and Large!
Martin Schmiedecker
 48:02
48:02Building Security Champions
Tanya Janca
 44:30
44:30Securing Your Web Application Pipeline From Intruders
Milecia McGregor
Related Articles
View all articles


.png?w=240&auto=compress,format)
From learning to earning
Jobs that call for the skills explored in this talk.







Excellence AG
Kotlin
Kubernetes
Apache Kafka
Microservices
Continuous Delivery
+1


e.solutions GmbH