Sebastian Leuer
Programming secure C#/.NET Applications: Dos & Don'ts
#1about 5 minutes
AI-generated code can introduce security risks
AI tools can generate insecure code by using deprecated APIs, introducing biases like modulo bias, or having incomplete logic, requiring a manual security review.
#2about 11 minutes
Handling character encoding to prevent spoofing attacks
Visually similar Unicode characters can be used to spoof identities in attacks, which can be mitigated by using ordinal string comparison instead of culture-invariant comparison.
#3about 12 minutes
Mitigating SQL, command, and path traversal injections
Untrusted user input can lead to various injection attacks, which are prevented by using parameterized SQL queries, the ArgumentList property for processes, and robust path validation.
#4about 4 minutes
Avoiding deserialization vulnerabilities in JSON and XML
Insecure default settings in parsers, like TypeNameHandling in Newtonsoft.Json or DTD processing in XML readers, can lead to remote code execution vulnerabilities.
Related jobs
Jobs that call for the skills explored in this talk.
Matching moments

02:26 MIN
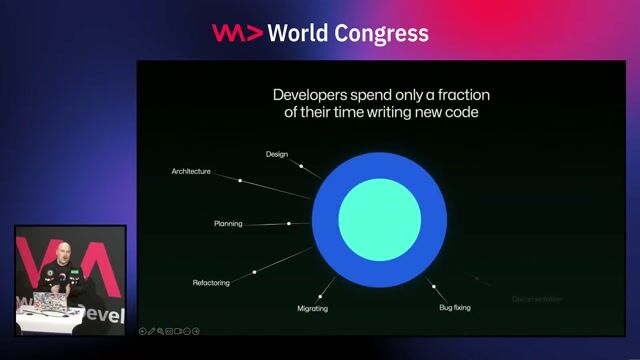
Why developers make basic cybersecurity mistakes
Don't Be A Naive Developer: How To Avoid Basic Cybersecurity Mistakes
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

06:10 MIN
Mitigating the security risks of AI-generated code
Developer Productivity Using AI Tools and Services - Ryan J Salva
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

07:10 MIN
Managing security risks of AI-assisted code generation
WWC24 - Chris Wysopal, Helmut Reisinger and Johannes Steger - Fighting Digital Threats in the Age of AI
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
01:31 MIN
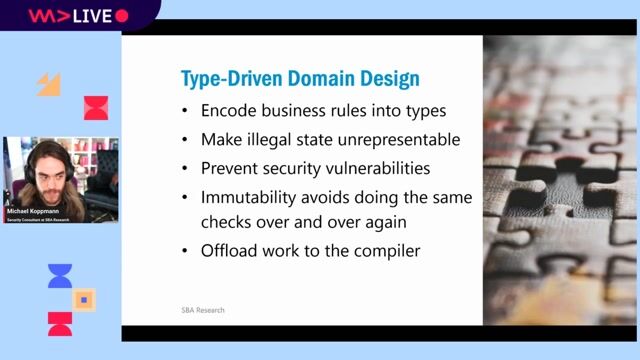
Key takeaways for building secure applications
Typed Security: Preventing Vulnerabilities By Design
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
03:27 MIN
Common security failures beyond individual coding errors
Maturity assessment for technicians or how I learned to love OWASP SAMM
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

05:37 MIN
Five common cybersecurity mistakes developers make
Don't Be A Naive Developer: How To Avoid Basic Cybersecurity Mistakes
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

04:18 MIN
The security risks of AI-generated code
A hundred ways to wreck your AI - the (in)security of machine learning systems
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

01:51 MIN
Final advice on security and responsible AI usage
WeAreDevelopers LIVE - Chrome for Sale? Comet - the upcoming perplexity browser Stealing and leaking
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
Featured Partners
Related Videos
 58:19
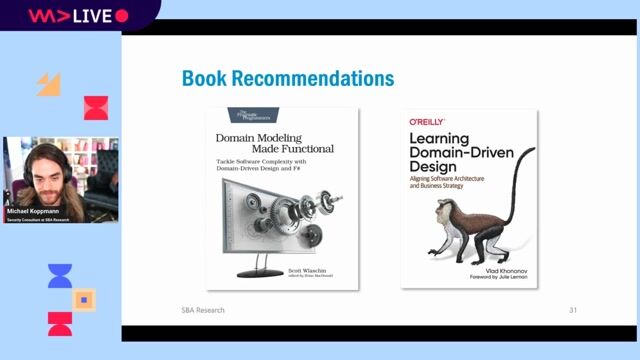
58:19Typed Security: Preventing Vulnerabilities By Design
Michael Koppmann
 28:41
28:41101 Typical Security Pitfalls
Alexander Pirker
 28:45
28:45How your .NET software supply chain is open to attack : and how to fix it
Andrei Epure
 28:01
28:01Don't Be A Naive Developer: How To Avoid Basic Cybersecurity Mistakes
Tino Sokic
 41:54
41:54Hacking C# from the inside - how to do anything in NET
Adam Furmanek
 29:50
29:50Real-World Security for Busy Developers
Kevin Lewis
 1:58:48
1:58:48Software Security 101: Secure Coding Basics
Thomas Konrad
 30:36
30:36The AI Security Survival Guide: Practical Advice for Stressed-Out Developers
Mackenzie Jackson
Related Articles
View all articles



From learning to earning
Jobs that call for the skills explored in this talk.


Vesterling Consulting GmbH
€70-90K
Software Architecture





Neumeier Gmbh & Co. Kg
MariaDB
SAP HANA
.NET Core
Machine Learning
Microsoft SQL Server

