Kevin Lewis
Real-World Security for Busy Developers
#1about 9 minutes
Why developers must take ownership of application security
The growing responsibility for security falls on developers due to the high cost of breaches and the scarcity of dedicated security specialists.
#2about 3 minutes
Prevent leaked secrets with push protection and scanning
GitHub's push protection blocks credentials from being committed, while secret scanning finds existing keys across your entire repository history.
#3about 9 minutes
Write and review secure code using AI-powered tools
Use GitHub Copilot for security education and code reviews, while CodeQL automatically finds vulnerabilities that Copilot Autofix can then resolve.
#4about 5 minutes
Manage vulnerable dependencies in your software supply chain
Use dependency review to check for vulnerabilities and license compliance in pull requests, and let Dependabot proactively create fixes for you.
#5about 1 minute
Drive security fixes with organization-wide campaigns
Security campaigns allow teams to prioritize and track the remediation of specific vulnerabilities across all repositories in an organization.
#6about 3 minutes
How security tools integrate into the developer workflow
A summary of how tools like push protection, code scanning, and Dependabot fit seamlessly into each stage of development from the IDE to production.
Related jobs
Jobs that call for the skills explored in this talk.
Matching moments
03:55 MIN
Avoiding common security mistakes and giving better feedback
The weekly developer show: Boosting Python with CUDA, CSS Updates & Navigating New Tech Stacks
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

02:43 MIN
Integrating security earlier in the development lifecycle
Vulnerable VS Code extensions are now at your front door
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
03:27 MIN
Common security failures beyond individual coding errors
Maturity assessment for technicians or how I learned to love OWASP SAMM
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
02:28 MIN
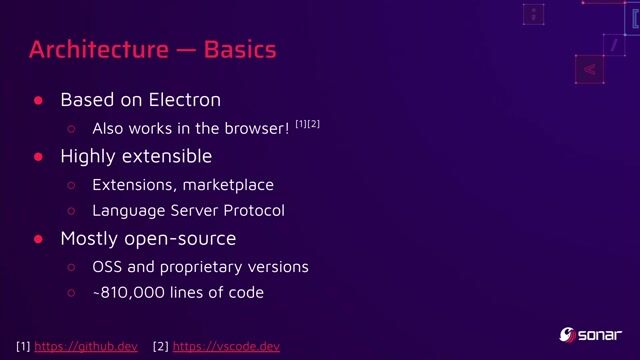
Key takeaways on IDE and developer tool security
You click, you lose: a practical look at VSCode's security
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
04:40 MIN
Integrating security throughout the CI/CD process
Plan CI/CD on the Enterprise level!
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

05:06 MIN
Hardening the CI/CD pipeline with automated security tools
You can’t hack what you can’t see
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
02:23 MIN
Key strategies for building a secure code culture
Secure Code Superstars: Empowering Developers and Surpassing Security Challenges Together
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

02:46 MIN
Why shift left security is crucial for modern development
Real-world Threat Modeling
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
Featured Partners
Related Videos
 25:28
25:28How GitHub secures open source
Joseph Katsioloudes
 21:53
21:53Simple Steps to Kill DevSec without Giving Up on Security
Isaac Evans
 22:18
22:18Why Security-First Development Helps You Ship Better Software Faster
Michael Wildpaner
 24:47
24:47Supply Chain Security and the Real World: Lessons From Incidents
Adrian Mouat
 23:34
23:34Secure Code Superstars: Empowering Developers and Surpassing Security Challenges Together
Stefania Chaplin
 33:29
33:29Programming secure C#/.NET Applications: Dos & Don'ts
Sebastian Leuer
 29:47
29:47You click, you lose: a practical look at VSCode's security
Thomas Chauchefoin & Paul Gerste
 44:30
44:30Securing Your Web Application Pipeline From Intruders
Milecia McGregor
Related Articles
View all articles
.png?w=240&auto=compress,format)


From learning to earning
Jobs that call for the skills explored in this talk.



NTT DATA Deutschland GmbH
Remote
Node.js
Continuous Integration

NTT DATA Deutschland GmbH
Remote
Node.js
Continuous Integration

e.solutions GmbH


GULP Information Services GmbH
Remote
Flutter
Routing
Continuous Integration


Vesterling Consulting GmbH
€70-90K
Software Architecture