Isaac Evans
Simple Steps to Kill DevSec without Giving Up on Security
#1about 5 minutes
The corrosive effect of false positives in security tools
Traditional code scanners overwhelm developers with a high rate of false positives, eroding trust and causing important alerts to be ignored.
#2about 1 minute
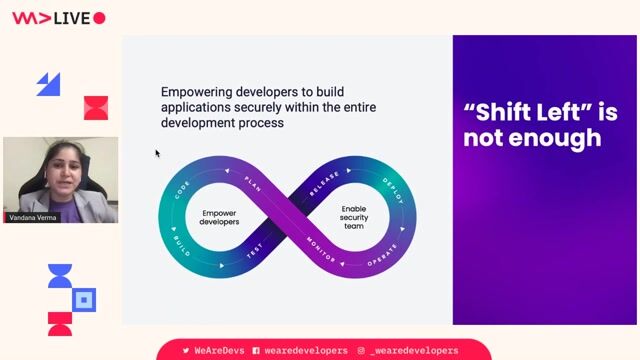
Why the original "shift left" security movement failed
The shift left movement often failed because it simply redirected a high-noise firehose of security alerts from security teams to developers without improving signal quality.
#3about 1 minute
How Android and iOS successfully hardened their platforms
The significant increase in the market price for zero-day exploits for Android and iOS demonstrates their success in making software more expensive to hack.
#4about 6 minutes
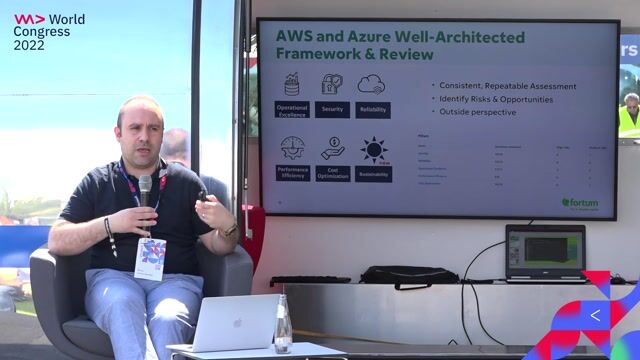
Adopting a secure guardrails over security gates mindset
Effective security programs use secure guardrails, like providing secure defaults and actionable fixes, to guide developers without blocking their workflow.
#5about 3 minutes
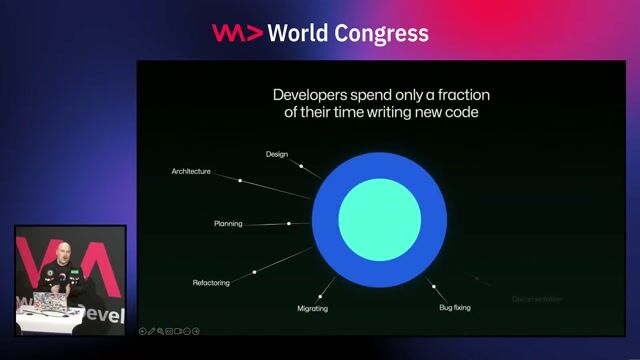
Prioritize securing new code over fixing the backlog
Since vulnerabilities are exponentially more likely to be found in new code, focusing security efforts there provides a greater return than trying to fix the entire existing backlog.
#6about 3 minutes
The ROI of basic security training and securing LLMs
Elevating developers to a basic level of security awareness yields the largest reduction in vulnerabilities, a principle that now extends to securing code generated by LLMs.
#7about 3 minutes
A practical formula for an effective AppSec program
An application security program's effectiveness is a product of its components, where a poor signal-to-noise ratio can nullify all other efforts.
Related jobs
Jobs that call for the skills explored in this talk.
Matching moments
01:33 MIN
Shifting security testing left in the development lifecycle
Vue3 practical development
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

04:29 MIN
The modern DevSecOps approach to application security
Maturity assessment for technicians or how I learned to love OWASP SAMM
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

03:15 MIN
Scaling AppSec teams by empowering developers
Why Security-First Development Helps You Ship Better Software Faster
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
08:08 MIN
How to shift left with a security champions program
Stranger Danger: Your Java Attack Surface Just Got Bigger
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
03:08 MIN
Shifting security left with collaborative threat modeling
We adopted DevOps and are Cloud-native, Now What?
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

04:25 MIN
Balancing developer and stakeholder security priorities
What The Hack is Web App Sec?
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

00:45 MIN
Addressing developer friction in application security
Get security done: streamlining application security with Aikido
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

02:26 MIN
Why developers make basic cybersecurity mistakes
Don't Be A Naive Developer: How To Avoid Basic Cybersecurity Mistakes
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
Featured Partners
Related Videos
 29:50
29:50Real-World Security for Busy Developers
Kevin Lewis
 22:18
22:18Why Security-First Development Helps You Ship Better Software Faster
Michael Wildpaner
 23:34
23:34Secure Code Superstars: Empowering Developers and Surpassing Security Challenges Together
Stefania Chaplin
 08:27
08:27Get security done: streamlining application security with Aikido
Mia Neethling
 25:28
25:28How GitHub secures open source
Joseph Katsioloudes
 16:00
16:00DevSecOps culture
Ali Yazdani
 24:47
24:47Supply Chain Security and the Real World: Lessons From Incidents
Adrian Mouat
 27:32
27:32Security Pitfalls for Software Engineers
Jasmin Azemović
Related Articles
View all articles
.png?w=240&auto=compress,format)


From learning to earning
Jobs that call for the skills explored in this talk.


NTT DATA Deutschland GmbH
Remote
Node.js
Continuous Integration

NTT DATA Deutschland GmbH
Remote
Node.js
Continuous Integration





