Davor Frkat
Automotive Security Challenges: A Supplier's View
#1about 5 minutes
Understanding the role of a Tier 1 automotive supplier
Bosch Engineering operates as a key supplier for diverse mobility sectors, integrating cybersecurity into custom components and vehicle concepts.
#2about 8 minutes
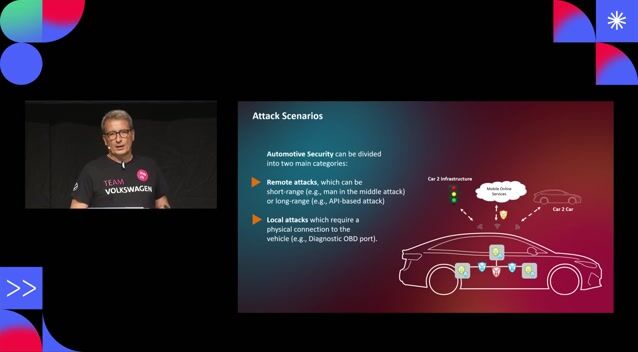
An overview of the automotive security landscape
The increasing connectivity in modern vehicles expands the attack surface, creating significant safety risks and data privacy concerns.
#3about 5 minutes
Learning from historical and recent vehicle attacks
Analyzing past incidents like the Jeep Cherokee hack and current CAN bus injection exploits reveals how attackers can gain physical and remote control of vehicles.
#4about 7 minutes
Hardware limitations and secure communication challenges
Long hardware lifecycles and resource constraints create significant challenges for implementing features like secure onboard communication (SecOC) with its strict latency requirements.
#5about 7 minutes
New threats from modern vehicle E/E architectures
The trend toward centralized, software-defined vehicles using containers and hypervisors increases complexity and introduces new threats like ransomware.
#6about 6 minutes
Managing keys and updates over the vehicle lifetime
Suppliers face significant challenges in managing cryptographic keys and preserving software build chains to deliver secure updates for over 15 years.
#7about 2 minutes
Preparing for the threat of post-quantum cryptography
The industry must plan for post-quantum cryptography now to protect vehicles that will still be on the road when current algorithms are broken.
#8about 5 minutes
Adhering to automotive security standards and regulations
Regulations like ISO 21434 and UNECE R155 drive security processes, requiring suppliers to establish vulnerability management programs and support OEMs in achieving vehicle type approval.
#9about 5 minutes
Security challenges of autonomous driving and forensics
Autonomous vehicles require tight co-engineering of safety and security, along with new capabilities for digital forensics to investigate incidents.
Related jobs
Jobs that call for the skills explored in this talk.
Matching moments

03:18 MIN
The role of security in specialized vehicle projects
Cyber Security: Small, and Large!
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
02:58 MIN
Volkswagen's approach to in-vehicle network security
Cybersecurity for Software Defined Vehicles
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

03:11 MIN
Managing security over the entire vehicle lifecycle
Cybersecurity for Software Defined Vehicles
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
04:00 MIN
Exploring the security vulnerabilities of connected cars
Using all the HTML, Running State of the Browser and "Modern" is Rubbish
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
03:18 MIN
Q&A on securing CAN bus and future architectures
Cybersecurity for Software Defined Vehicles
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
02:32 MIN
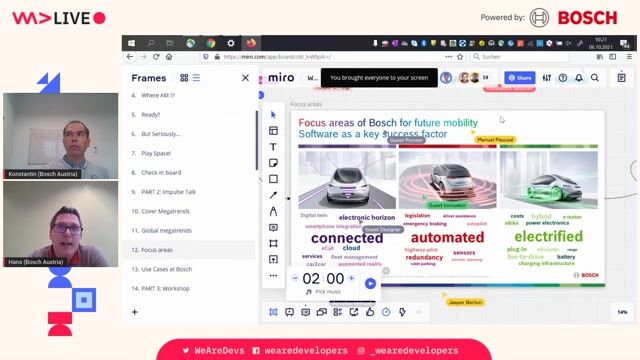
Bosch's strategy for connected, automated, and electrified vehicles
On developing smartphones on wheels
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
01:57 MIN
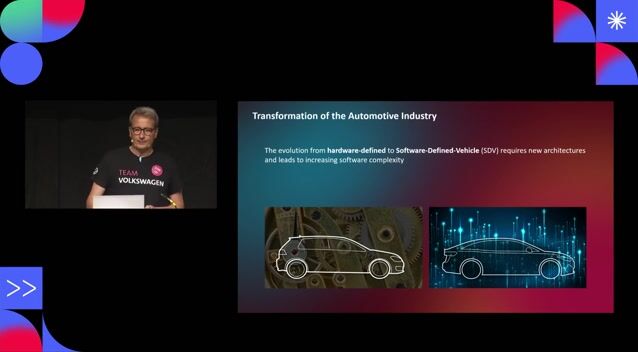
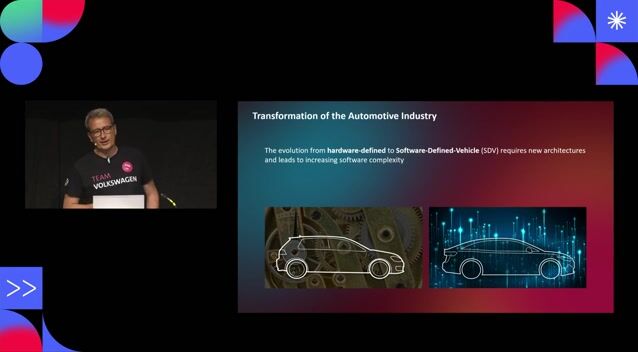
The automotive industry's shift to software-defined vehicles
Cybersecurity for Software Defined Vehicles
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
06:22 MIN
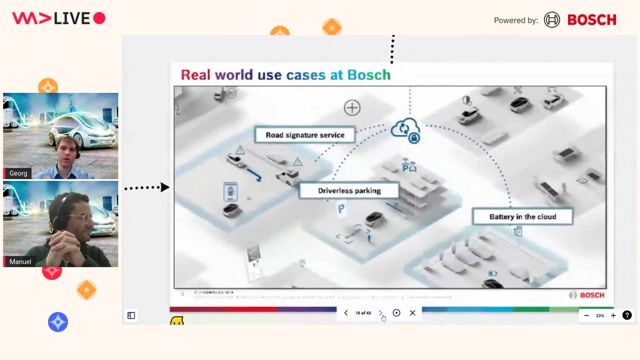
Exploring real-world automotive use cases from Bosch
The future of automotive mobility: Upcoming E/E architectures, V2X and its challenges
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
Featured Partners
Related Videos
 37:32
37:32Cyber Security: Small, and Large!
Martin Schmiedecker
 22:09
22:09Cybersecurity for Software Defined Vehicles
Henning Harbs
 37:36
37:36Walking into the era of Supply Chain Risks
Vandana Verma
 29:34
29:34You can’t hack what you can’t see
Reto Kaeser
 41:03
41:03The best of two worlds - Bringing enterprise-grade Linux to the vehicle
Joachim Werner
 1:51:43
1:51:43On developing smartphones on wheels
Hans-Jürgen Eidler
 1:47:33
1:47:33The future of automotive mobility: Upcoming E/E architectures, V2X and its challenges
Georg Kühberger & Manuel Pascual
 21:49
21:49A Hitchhikers Guide to Container Security - Automotive Edition 2024
Reinhard Kugler
Related Articles
View all articles

.gif?w=240&auto=compress,format)
.png?w=240&auto=compress,format)
From learning to earning
Jobs that call for the skills explored in this talk.



e.solutions GmbH



Avantgarde Experts GmbH
Remote
Network Security
Software Architecture


Manndeckung GmbH
Schozach-Bottwartal GVV, Germany

dspace digital signal processing and control engineering GmbH
Remote
GIT
Linux
DevOps