Vandana Verma
Walking into the era of Supply Chain Risks
#1about 4 minutes
Developers as an unintentional malware distribution vehicle
Recent incidents like the event-stream package compromise show how attackers can turn developers into a distribution channel for malware.
#2about 4 minutes
The hidden risks of open-source dependencies
Vulnerabilities in common dependencies, like Apache Struts which led to the Equifax breach, highlight the danger of unmanaged open-source code.
#3about 4 minutes
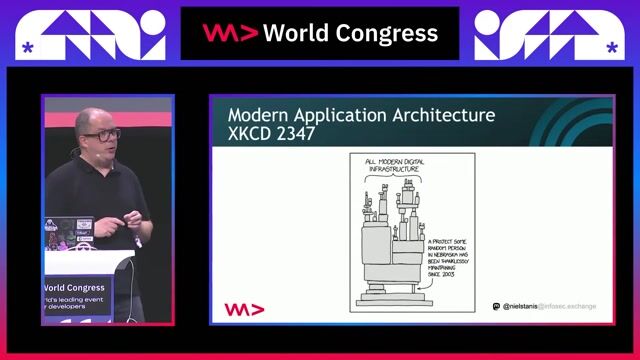
Defining the modern software supply chain
The software supply chain mirrors a manufacturing process, and attackers exploit its weakest links to create cascading failures.
#4about 4 minutes
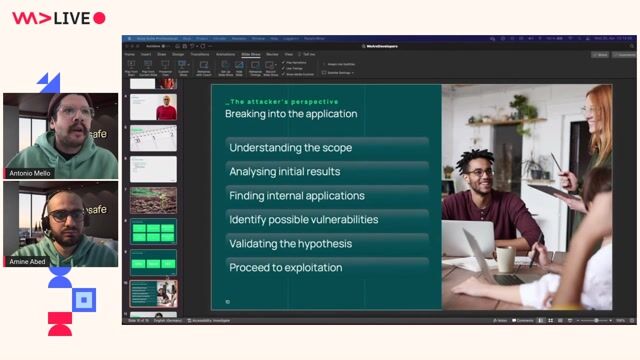
Common attack vectors and the zero trust principle
Attacks like dependency confusion and prototype pollution, exemplified by the SolarWinds incident, necessitate a zero trust security model.
#5about 4 minutes
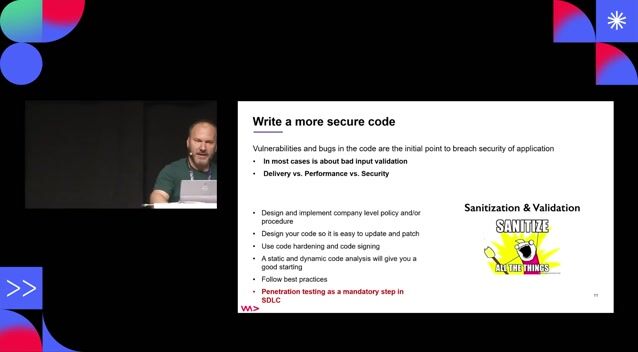
Building a foundation for pipeline security
Secure your development pipeline by using frameworks from OpenSSF, implementing SBOMs, and securing code, containers, and secrets.
#6about 4 minutes
Demo: Bypassing sanitization with prototype pollution
A practical demonstration shows how prototype pollution can bypass input validation in a Node.js application by passing an array instead of a string.
#7about 3 minutes
Demo: Exploiting the Log4Shell vulnerability
This live hacking demo shows how the Log4j (Log4Shell) vulnerability allows an attacker to achieve remote code execution on a vulnerable server.
#8about 2 minutes
Demo: Remote code execution via a Python dependency
A vulnerable version of the Python Celery library is exploited to achieve remote code execution and exfiltrate server information.
#9about 1 minute
Fostering a developer-first security culture
The key to better security is creating a developer-friendly environment and engaging with communities like OWASP to stay informed.
#10about 8 minutes
Q&A: Career advice for aspiring security professionals
The speaker shares her career journey, tips for students entering cybersecurity, and thoughts on social engineering and learning resources.
Related jobs
Jobs that call for the skills explored in this talk.
Matching moments
04:45 MIN
Mitigating supply chain attacks with DevSecOps practices
Security Pitfalls for Software Engineers
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

05:49 MIN
Common attacks targeting software developers
Vulnerable VS Code extensions are now at your front door
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
03:43 MIN
Modern cybersecurity challenges for developers
Cyber Security: Small, and Large!
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

06:19 MIN
Understanding the risks of the modern software supply chain
Overcome your trust issues! In a world of fake data, Data Provenance FTW
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
05:43 MIN
How attackers exploit developers and packages
Vue3 practical development
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

01:46 MIN
Understanding the rising threat to software supply chains
Open Source Secure Software Supply Chain in action
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

04:54 MIN
Why developers are a prime target for attackers
You click, you lose: a practical look at VSCode's security
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
03:40 MIN
Understanding the inherent risks of third-party dependencies
Reviewing 3rd party library security easily using OpenSSF Scorecard
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
Featured Partners
Related Videos
 1:58:59
1:58:59Stranger Danger: Your Java Attack Surface Just Got Bigger
Vandana Verma Sehgal
 2:08:06
2:08:06The attacker's footprint
Antonio de Mello & Amine Abed
 44:30
44:30Securing Your Web Application Pipeline From Intruders
Milecia McGregor
 29:34
29:34You can’t hack what you can’t see
Reto Kaeser
 33:20
33:20DevSecOps: Security in DevOps
Aarno Aukia
 40:38
40:38How to Cause (or Prevent) a Massive Data Breach- Secure Coding and IDOR
Anna Bacher
 51:41
51:41Climate vs. Weather: How Do We Sustainably Make Software More Secure?
Panel Discussion
 32:55
32:55Open Source Secure Software Supply Chain in action
Natale Vinto
Related Articles
View all articles.gif?w=240&auto=compress,format)



From learning to earning
Jobs that call for the skills explored in this talk.






Westhouse Consulting GmbH
Intermediate
JUnit
Gitlab
Docker
Kubernetes
Apache Kafka
+3


Schwarz Dienstleistung KG
NoSQL
Vue.js
Kotlin
Docker
Kubernetes
+1

Swisscard Aecs Gmbh
Terraform
Kubernetes
Continuous Integration