Chloé Messdaghi
We Deserve Rights
#1about 3 minutes
The legal risks facing ethical security researchers
Good-faith hackers face prosecution and fear due to a lack of legal protections for their work in securing systems.
#2about 1 minute
Defining the difference between a hacker and an attacker
The key distinction between a hacker who protects and an attacker who exploits is their intent, not their skillset.
#3about 4 minutes
A case study of a bug bounty program gone wrong
A security researcher who reported a bug to DJI was threatened with a lawsuit, highlighting the risks of poorly managed disclosure programs.
#4about 9 minutes
How social constructs and fear shape public perception
Media portrayals create socially constructed beliefs that trigger fear-based responses towards hackers, which can be overcome with personal stories.
#5about 7 minutes
Practical ways to correct media misrepresentation of hackers
Combat negative stereotypes by kindly correcting inaccurate terminology and imagery used by journalists and marketers.
#6about 5 minutes
The dangers of the Computer Fraud and Abuse Act (CFAA)
The vague and outdated CFAA is misused by companies to prosecute ethical hackers, as tragically exemplified by the case of Aaron Swartz.
#7about 1 minute
How to advocate for legislative change and reform
Individuals can drive legislative reform by voting, identifying their local representatives, and collaborating with advocacy groups to schedule meetings.
#8about 3 minutes
Best practices for vulnerability disclosure policies
Companies can build trust and improve security by creating clear vulnerability disclosure policies with defined scope, simple language, and a dedicated contact.
#9about 2 minutes
A final call to action for the community
Change starts with individual awareness and action, such as supporting advocacy organizations and sharing personal stories to challenge stereotypes.
#10about 8 minutes
Q&A on reclaiming the term hacker and corporate lobbying
The community prefers the term "hacker" to reclaim its identity, while corporate lobbying from tech companies actively prevents reforms to the CFAA.
Related jobs
Jobs that call for the skills explored in this talk.
Matching moments

05:31 MIN
From vulnerability researcher to automated security founder
The transformative impact of GenAI for software development and its implications for cybersecurity
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

02:26 MIN
Why developers make basic cybersecurity mistakes
Don't Be A Naive Developer: How To Avoid Basic Cybersecurity Mistakes
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

03:35 MIN
Exploring the need for regulation in software development
Climate vs. Weather: How Do We Sustainably Make Software More Secure?
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

02:26 MIN
Understanding attacker motivations and barriers
Cyber Security: Small, and Large!
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
09:15 MIN
Q&A on blockchain, pentesting, and ethical implications
Reverse Vending Machine (RVM) Security: Real World Exploits / Vulnerabilities
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
02:28 MIN
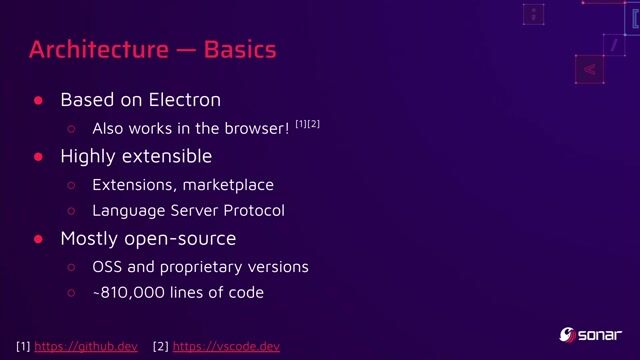
Key takeaways on IDE and developer tool security
You click, you lose: a practical look at VSCode's security
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

27:22 MIN
Q&A on social engineering and a career in security
Stranger Danger: Your Java Attack Surface Just Got Bigger
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

08:18 MIN
Q&A: Career advice for aspiring security professionals
Walking into the era of Supply Chain Risks
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
Featured Partners
Related Videos
 43:56
43:56Getting under the skin: The Social Engineering techniques
Mauro Verderosa
 37:32
37:32Cyber Security: Small, and Large!
Martin Schmiedecker
 40:38
40:38How to Cause (or Prevent) a Massive Data Breach- Secure Coding and IDOR
Anna Bacher
 29:34
29:34You can’t hack what you can’t see
Reto Kaeser
 27:36
27:36Unleashing the Power of Developers: Why Cybersecurity is the Missing Piece?!?
Tino Sokic
 27:32
27:32Security Pitfalls for Software Engineers
Jasmin Azemović
 24:23
24:23A hundred ways to wreck your AI - the (in)security of machine learning systems
Balázs Kiss
 29:47
29:47You click, you lose: a practical look at VSCode's security
Thomas Chauchefoin & Paul Gerste
Related Articles
View all articles


.png?w=240&auto=compress,format)
From learning to earning
Jobs that call for the skills explored in this talk.

freiheit.com freiheit.com
Remote
Unix
Docker
Terraform
Kubernetes
+1






Ernst & Young
Amsterdam, Netherlands
Remote
€6K
Junior
Data analysis


Hochschule Luzern