Alex Olivier
Un-complicate authorization maintenance
#1about 2 minutes
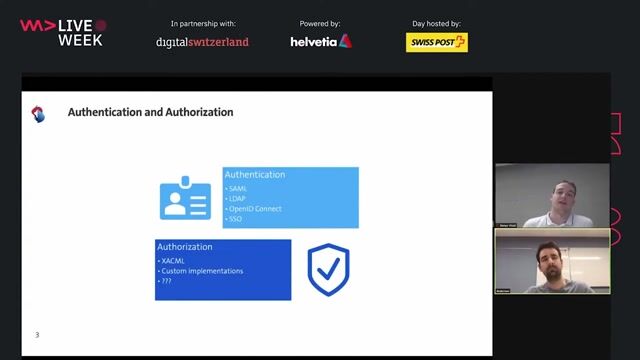
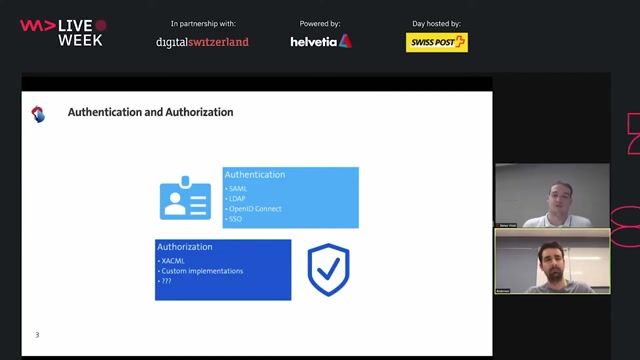
Differentiating between authentication and authorization
Authentication verifies a user's identity, while authorization determines what actions that verified user is allowed to perform.
#2about 15 minutes
How authorization logic evolves into spaghetti code
As a product grows, simple role checks escalate into complex, hardcoded logic for packaging, regions, enterprise features, and compliance, creating a maintenance bottleneck.
#3about 2 minutes
Why microservices exacerbate authorization maintenance issues
In a microservices architecture, authorization logic must be re-implemented and maintained across multiple services, languages, and teams, increasing complexity and risk.
#4about 5 minutes
A modern approach using a decoupled authorization service
Decoupling authorization logic into a central, policy-based service separates it from application code, enabling independent evolution and management.
#5about 8 minutes
Implementing decoupled authorization with the sidecar pattern
Deploying the authorization service as a sidecar in Kubernetes co-locates it with your application for low-latency checks while keeping the logic centralized.
#6about 3 minutes
Evaluating the advantages and disadvantages of decoupling
Decoupling provides centralized logic, language agnosticism, and consistent audit trails, but requires managing an additional service and potentially learning a new DSL.
#7about 1 minute
Using the open source project Cerbos for authorization
Cerbos is an open-source, self-hosted authorization service that implements the decoupled, policy-based approach for managing complex permissions.
#8about 19 minutes
Answering audience questions on authorization best practices
The discussion covers implementing authorization at different OSI layers, ensuring changes are tested, identifying complexity, and handling compromised credentials.
Related jobs
Jobs that call for the skills explored in this talk.
Matching moments
03:06 MIN
The challenges of embedding authorization in application code
Decoupled Authorization using Policy as Code
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

01:57 MIN
The challenges of traditional in-code authorization logic
Keymate – Modern Authorization for Developers
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

00:53 MIN
Externalizing authorization with service mesh and API gateways
Keymate – Modern Authorization for Developers
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
05:39 MIN
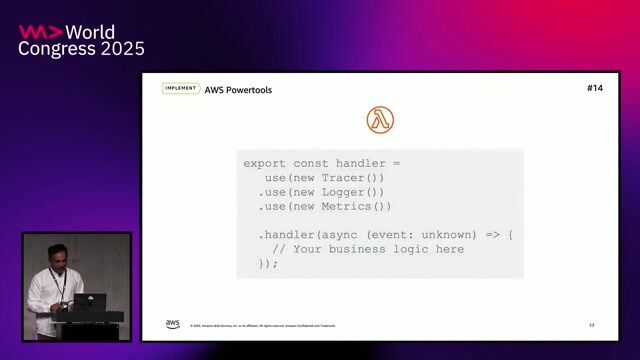
Enhancing applications with observability and authorization
30 powerful AWS hacks in just 30 minutes: Boost your developer productivity
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
06:29 MIN
Introducing Policy as Code and Open Policy Agent
Decoupled Authorization using Policy as Code
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
04:16 MIN
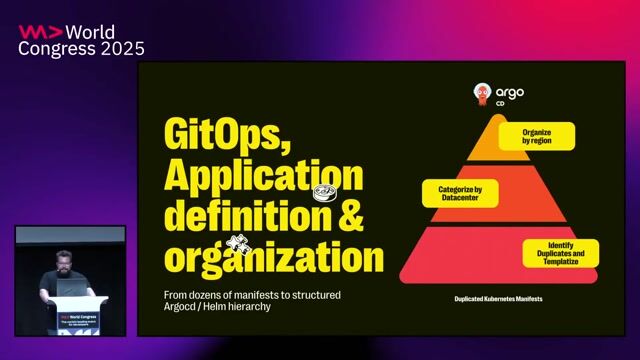
Enabling developer autonomy with GitOps and CRDs
Software Engineering Social Connection: Yubo’s lean approach to scaling an 80M-user infrastructure
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
03:11 MIN
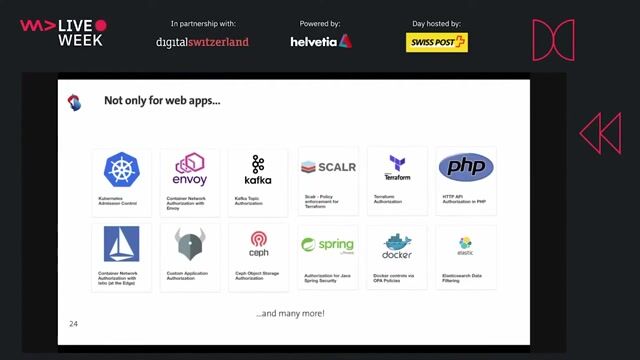
Exploring other use cases for OPA beyond web APIs
Decoupled Authorization using Policy as Code
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

01:21 MIN
Automating policy enforcement with admission controllers
Kubernetes Security Best Practices
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
Featured Partners
Related Videos
 32:16
32:16Decoupled Authorization using Policy as Code
Anderson Dadario & Denys Vitali
 45:19
45:19Security Challenges of Breaking A Monolith
Reinhard Kugler
 29:31
29:31Break the Chain: Decentralized solutions for today’s Web2.0 privacy problems
Adam Larter
 29:34
29:34You can’t hack what you can’t see
Reto Kaeser
 58:19
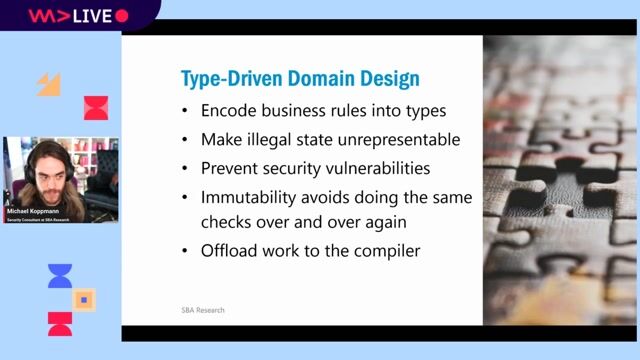
58:19Typed Security: Preventing Vulnerabilities By Design
Michael Koppmann
 33:20
33:20DevSecOps: Security in DevOps
Aarno Aukia
 06:04
06:04Keymate – Modern Authorization for Developers
Halil Özkan
 40:38
40:38How to Cause (or Prevent) a Massive Data Breach- Secure Coding and IDOR
Anna Bacher
Related Articles
View all articles



From learning to earning
Jobs that call for the skills explored in this talk.

Peter Park System GmbH
München, Germany
Senior
Python
Docker
Node.js
JavaScript



SMG Swiss Marketplace Group
Canton de Valbonne, France
Senior

GULP Information Services GmbH
GIT
Next.js
TypeScript
AWS Lambda
Amazon DynamoDB
+1



Cosonic GmbH
Remote
€60-80K
Senior
Docker
PostgreSQL
Kubernetes
+2
