Jovan Zivanovic
Reverse Vending Machine (RVM) Security: Real World Exploits / Vulnerabilities
#1about 3 minutes
The financial incentive for hacking reverse vending machines
Reverse vending machines present a security risk because they exchange returned bottles for money, creating an opportunity for financial exploits.
#2about 4 minutes
Understanding the bottle detection and refund process
RVMs use a combination of sensors like barcode scanners, weight sensors, shape detectors, and material analysis to validate and process returned bottles.
#3about 4 minutes
Categorizing common reverse vending machine attack vectors
Attacks on RVMs fall into three main categories: insider manipulation, tricking the bottle acceptance system, and misclassifying bottles for higher payouts.
#4about 4 minutes
Analyzing supermarket receipts to find security flaws
By collecting and comparing receipts from different supermarket chains, researchers identified patterns in barcode generation to find potential vulnerabilities.
#5about 4 minutes
Discovering a predictable and static barcode vulnerability
One supermarket chain used a static EAN-13 barcode on receipts where the refund amount was directly encoded, making it easy to forge.
#6about 2 minutes
Forging a valid receipt with a script and printer
A simple script and a thermal printer can generate a forged receipt with a custom refund amount that is accepted by the store's checkout system.
#7about 2 minutes
The vendor response to the disclosed vulnerability
The RVM manufacturer confirmed the vulnerability and stated that the secure, cloud-validated solution is an optional feature that customers must pay extra for.
#8about 3 minutes
Finding similar and new exploits in Finland's RVMs
An investigation in Finland revealed the same receipt forgery vulnerability, plus a new attack involving swapping barcode stickers on bottles to claim a higher refund.
#9about 2 minutes
Mitigating receipt fraud with a cloud validation system
The most effective way to prevent receipt forgery is to use a centralized data store that generates a unique ID for each receipt and invalidates it after one use.
#10about 9 minutes
Q&A on blockchain, pentesting, and ethical implications
The speaker discusses using blockchain for validation, the importance of early security involvement and pentesting, and the ethics of exploiting recycling systems.
Related jobs
Jobs that call for the skills explored in this talk.
Matching moments
03:04 MIN
Examining IDOR vulnerabilities in major companies
How to Cause (or Prevent) a Massive Data Breach- Secure Coding and IDOR
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

02:00 MIN
Addressing unique security risks in RAG systems
Beyond the Hype: Building Trustworthy and Reliable LLM Applications with Guardrails
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
14:52 MIN
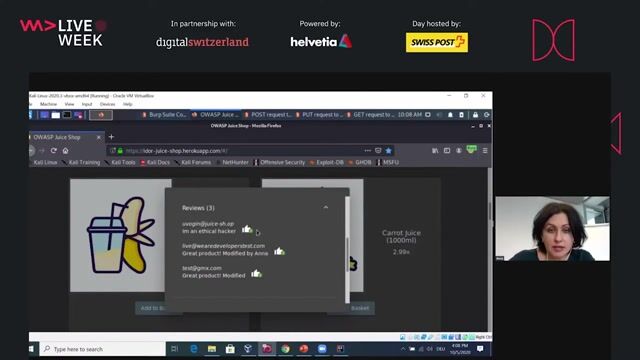
A practical demonstration of exploiting IDOR vulnerabilities
How to Cause (or Prevent) a Massive Data Breach- Secure Coding and IDOR
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
03:27 MIN
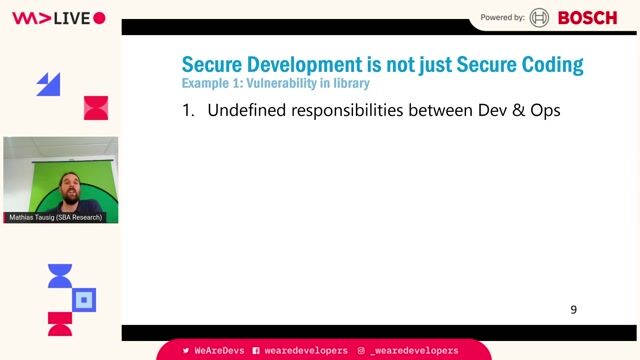
Common security failures beyond individual coding errors
Maturity assessment for technicians or how I learned to love OWASP SAMM
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

05:31 MIN
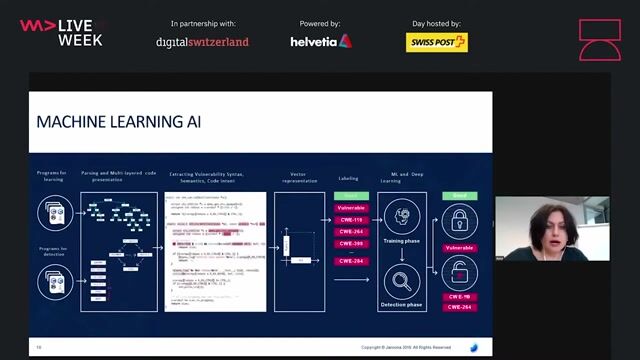
From vulnerability researcher to automated security founder
The transformative impact of GenAI for software development and its implications for cybersecurity
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

05:38 MIN
Why attackers use prompt injection techniques
Manipulating The Machine: Prompt Injections And Counter Measures
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
02:13 MIN
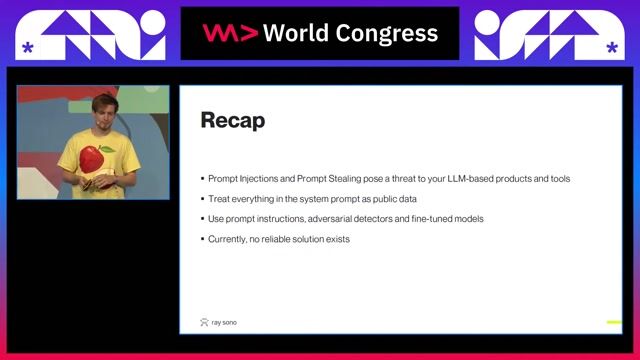
Key takeaways on prompt injection security
Manipulating The Machine: Prompt Injections And Counter Measures
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

05:09 MIN
Securing against AI-driven supply chain attacks
WeAreDevelopers LIVE: What's happening to React?, All-in-one editors, Fireships and Firebases & more
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
Featured Partners
Related Videos
 37:32
37:32Cyber Security: Small, and Large!
Martin Schmiedecker
 43:56
43:56Getting under the skin: The Social Engineering techniques
Mauro Verderosa
 40:38
40:38How to Cause (or Prevent) a Massive Data Breach- Secure Coding and IDOR
Anna Bacher
 2:08:06
2:08:06The attacker's footprint
Antonio de Mello & Amine Abed
 45:19
45:19Security Challenges of Breaking A Monolith
Reinhard Kugler
 57:47
57:47Cracking the Code: Decoding Anti-Bot Systems!
Fabien Vauchelles
 58:19
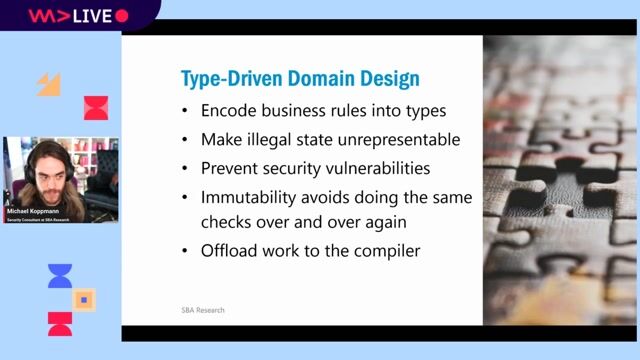
58:19Typed Security: Preventing Vulnerabilities By Design
Michael Koppmann
 29:47
29:47You click, you lose: a practical look at VSCode's security
Thomas Chauchefoin & Paul Gerste
Related Articles
View all articles
.png?w=240&auto=compress,format)


From learning to earning
Jobs that call for the skills explored in this talk.

Peter Park System GmbH
München, Germany
Intermediate
Senior
Bash
Linux
Python

Saby Company Page
Sarajevo, Bosnia and Herzegovina
Remote
€40-45K
Junior
Ruby on Rails
Microsoft SQL Server
Google Cloud Platform
+2


Valora Food Service Deutschland GmbH

Vesterling Consulting GmbH
€70-90K
Software Architecture


SVA System Vertrieb Alexander GmbH
Splunk

SVA System Vertrieb Alexander GmbH
Splunk
Data analysis

Fraunhofer-Gesellschaft