Liz Moy
This Machine Ends Data Breaches
#1about 4 minutes
Data breaches are a persistent threat for all companies
Even the largest tech companies suffer from data breaches, highlighting the need for a new approach to security like confidential computing.
#2about 5 minutes
Understanding trusted execution environments (TEEs)
A TEE is a secure, hardware-isolated enclave within a CPU that protects data while it is being processed in memory.
#3about 4 minutes
The three pillars of confidential computing
Confidential computing relies on data confidentiality, data integrity, and remote attestation to provide verifiable security for workloads.
#4about 9 minutes
How remote attestation verifies workload integrity
Attestation is a cryptographic process that proves a TEE has not been tampered with before any sensitive data is sent to it.
#5about 6 minutes
Exploring the confidential computing ecosystem
Major hardware vendors like Intel, AMD, and Nvidia, along with cloud providers, offer a growing ecosystem of TEE-enabled products and services.
#6about 5 minutes
Practical applications and use cases for TEEs
TEEs can be used to process PII, secure credentials, run private ML models, protect IP, and enable multi-party collaboration on sensitive data.
#7about 3 minutes
Demo of a secure medical imaging AI model
This demo shows how to run an ML model for brain tumor detection inside an AWS Nitro Enclave to protect both the model and patient data.
#8about 2 minutes
Demo of a secure financial lending application
A simple mortgage application demonstrates how to isolate and protect sensitive financial calculations within a TEE while integrating with a standard web app.
#9about 7 minutes
The future outlook for confidential computing
While challenges like performance, cost, and side-channel risks exist, the goal is for confidential computing to become a ubiquitous security standard.
#10about 14 minutes
Q&A on implementation, strategy, and AI's impact
The speaker answers audience questions about successful implementations, integrating confidential computing into a security strategy, and the risks of AI in cybersecurity.
Related jobs
Jobs that call for the skills explored in this talk.
Matching moments
05:03 MIN
Understanding confidential computing and trusted execution environments
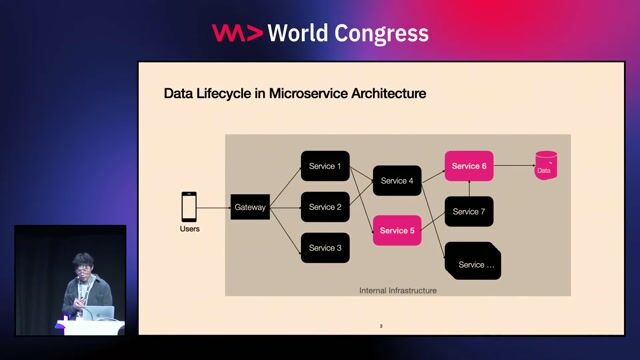
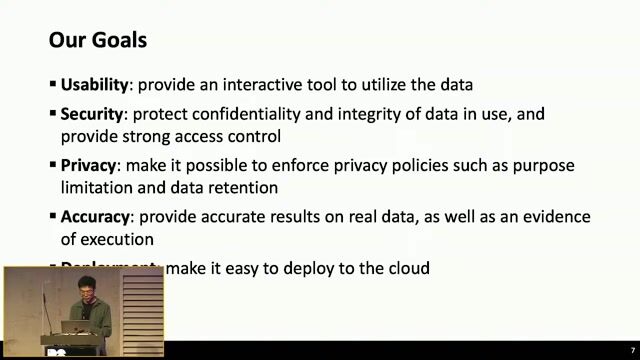
Safeguarding Sensitive Data Access At Scale with Privacy-Enhancing Technologies
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
02:16 MIN
How trusted execution environments enable secure collaboration
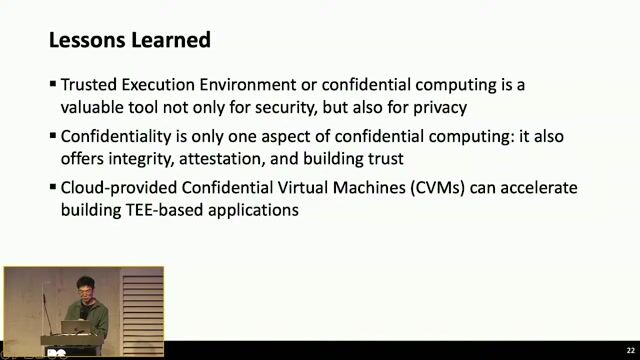
TikTok's Privacy Innovation
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

01:47 MIN
Building trusted environments for responsible AI
Bringing AI Everywhere
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

04:35 MIN
A solution combining serverless and confidential computing
Safeguarding Sensitive Data Access At Scale with Privacy-Enhancing Technologies
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
01:54 MIN
Learnings and future roadmap for the platform
TikTok's Privacy Innovation
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
02:41 MIN
Limitations of existing data privacy solutions
TikTok's Privacy Innovation
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

01:35 MIN
Summary of the data protection architecture
Safeguarding Sensitive Data Access At Scale with Privacy-Enhancing Technologies
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
02:28 MIN
Key takeaways on IDE and developer tool security
You click, you lose: a practical look at VSCode's security
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
Featured Partners
Related Videos
 29:34
29:34You can’t hack what you can’t see
Reto Kaeser
 56:06
56:06Stop Committing Your Secrets - GIt Hooks To The Rescue!
Dwayne McDaniel
 37:36
37:36Walking into the era of Supply Chain Risks
Vandana Verma
 40:38
40:38How to Cause (or Prevent) a Massive Data Breach- Secure Coding and IDOR
Anna Bacher
 45:19
45:19Security Challenges of Breaking A Monolith
Reinhard Kugler
 45:19
45:19Securing Frontend Applications with Trusted Types
Philippe De Ryck
 51:41
51:41Climate vs. Weather: How Do We Sustainably Make Software More Secure?
Panel Discussion
 37:32
37:32Cyber Security: Small, and Large!
Martin Schmiedecker
Related Articles
View all articles



From learning to earning
Jobs that call for the skills explored in this talk.

SYSKRON GmbH
Regensburg, Germany
Intermediate
Senior
.NET
Python
Kubernetes





NTT DATA Deutschland GmbH
Remote
Node.js
Continuous Integration

NTT DATA Deutschland GmbH
Remote
Node.js
Continuous Integration

