Mingshen Sun
Safeguarding Sensitive Data Access At Scale with Privacy-Enhancing Technologies
#1about 1 minute
The challenge of data security in microservice architectures
Microservice architectures offer scalability but create data protection challenges as sensitive data flows freely between many services.
#2about 5 minutes
Understanding confidential computing and trusted execution environments
Confidential computing uses hardware-based trusted execution environments (TEEs) to isolate data and code during processing, providing verifiable proof through remote attestation.
#3about 4 minutes
Key challenges of applying PETs at scale
Implementing privacy-enhancing technologies at scale is difficult due to microservice flexibility, the need for fine-grained purpose limitation, and providing verifiable transparency.
#4about 5 minutes
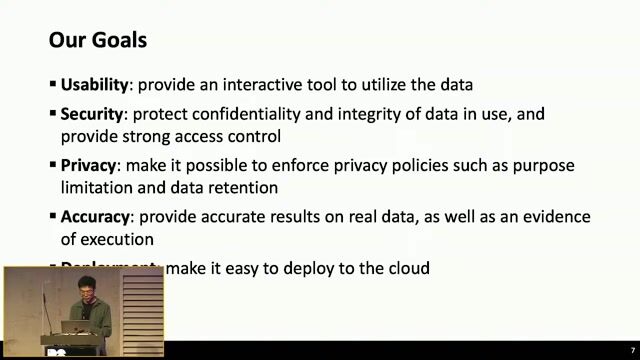
A solution combining serverless and confidential computing
A proposed architecture uses serverless computing to isolate sensitive data logic within a trusted execution environment, combined with pseudonymization for end-to-end protection.
#5about 4 minutes
Enabling third-party verification with remote attestation
Remote attestation allows third parties to verify workloads, enabling trusted management of key services like KMS and attestation services for hardware-backed access control.
#6about 2 minutes
Summary of the data protection architecture
The solution combines serverless computing, end-to-end data protection, and third-party verification to secure sensitive data in microservices while preserving flexibility.
Related jobs
Jobs that call for the skills explored in this talk.
Matching moments
02:42 MIN
Introducing a two-stage data clean room solution
TikTok's Privacy Innovation
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

05:06 MIN
Practical applications and use cases for TEEs
This Machine Ends Data Breaches
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
02:41 MIN
Limitations of existing data privacy solutions
TikTok's Privacy Innovation
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

04:24 MIN
Data breaches are a persistent threat for all companies
This Machine Ends Data Breaches
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

01:47 MIN
Building trusted environments for responsible AI
Bringing AI Everywhere
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

06:15 MIN
Exploring the confidential computing ecosystem
This Machine Ends Data Breaches
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
02:42 MIN
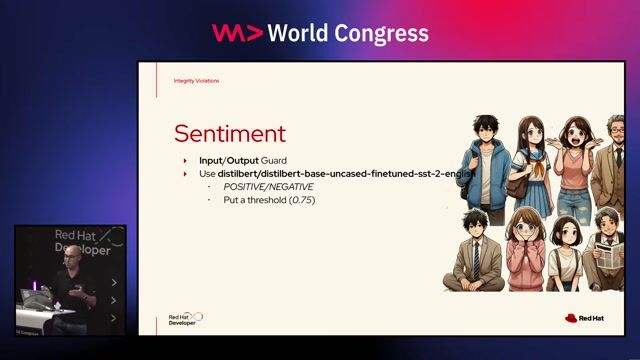
Protecting sensitive data with privacy guardrails
Beyond the Hype: Building Trustworthy and Reliable LLM Applications with Guardrails
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

11:25 MIN
Q&A on microservice architecture and security
Security Challenges of Breaking A Monolith
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
Featured Partners
Related Videos
 20:46
20:46TikTok's Privacy Innovation
Mingshen Sun
 59:34
59:34This Machine Ends Data Breaches
Liz Moy
 29:31
29:31Break the Chain: Decentralized solutions for today’s Web2.0 privacy problems
Adam Larter
 29:00
29:00Beyond the Hype: Building Trustworthy and Reliable LLM Applications with Guardrails
Alex Soto
 29:34
29:34You can’t hack what you can’t see
Reto Kaeser
 04:57
04:57Secure and Private AI - DeepMask
Hissan Usmani
 23:24
23:24Prompt Injection, Poisoning & More: The Dark Side of LLMs
Keno Dreßel
 28:30
28:30Empowering Developer Innovation - Balancing Speed, Security, and Scale
Amir Friedman, Martin Reynolds & Yair Etziony
Related Articles
View all articles


.gif?w=240&auto=compress,format)
From learning to earning
Jobs that call for the skills explored in this talk.








