Mathias Tausig
Turning Container security up to 11 with Capabilities
#1about 8 minutes
Demonstrating a man-in-the-middle attack between containers
A proof-of-concept shows how a malicious container can sniff unencrypted traffic between other containers running on the same host.
#2about 5 minutes
Introducing Linux capabilities for granular privilege control
Traditional Unix permissions are an all-or-nothing model, whereas Linux capabilities split root privileges into distinct units for finer control.
#3about 4 minutes
Differentiating between file and process capabilities
Capabilities can be set on files to elevate privileges for specific binaries or on processes to reduce them, with the latter being key for containers.
#4about 3 minutes
Managing default container capabilities in Docker
Docker grants a default set of powerful capabilities to containers, which can be restricted using `cap-drop` and `cap-add` flags.
#5about 4 minutes
Securing deployments by dropping unnecessary capabilities
By dropping all capabilities and only adding back the essential ones, the man-in-the-middle attack is successfully prevented in both Docker and Kubernetes.
#6about 3 minutes
Using capabilities as a defense-in-depth measure
Limiting capabilities does not prevent an initial exploit but significantly reduces the potential impact and blast radius of a compromised container.
Related jobs
Jobs that call for the skills explored in this talk.
Matching moments
01:22 MIN
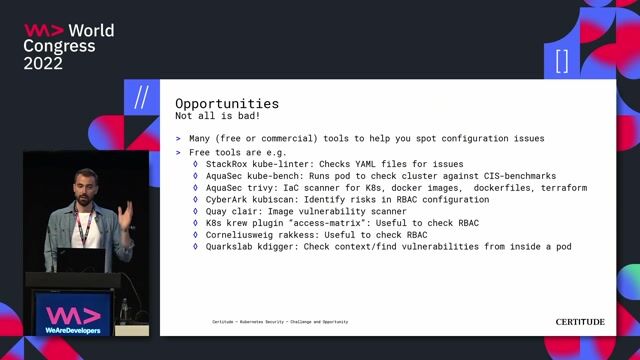
Leveraging containerization for improved security posture
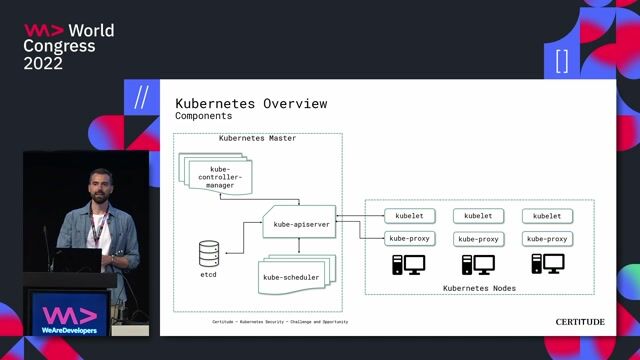
Kubernetes Security - Challenge and Opportunity
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
06:25 MIN
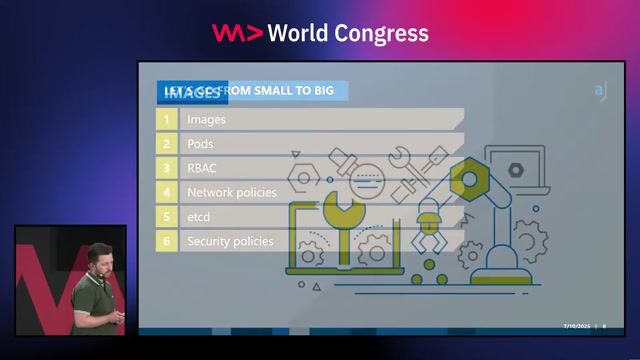
Security best practices for containers and Kubernetes
Microservices: how to get started with Spring Boot and Kubernetes
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
01:52 MIN
Securing container images and the software supply chain
Security Challenges of Breaking A Monolith
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
02:35 MIN
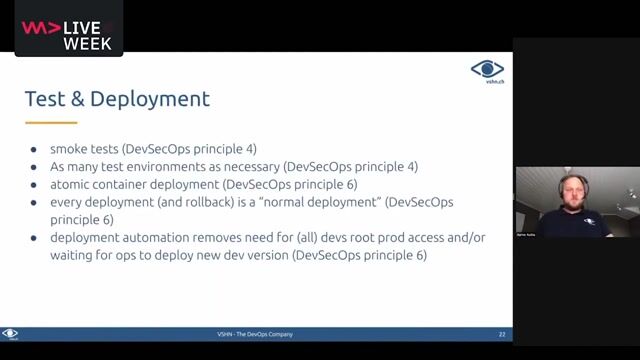
Using containers to improve security and deployment
DevSecOps: Security in DevOps
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
02:30 MIN
Securing container images against common vulnerabilities
Kubernetes Security Best Practices
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

05:08 MIN
Analyzing the impact of a container vulnerability
Security Challenges of Breaking A Monolith
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
01:35 MIN
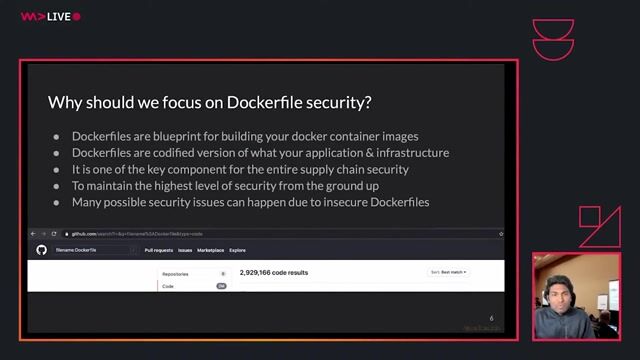
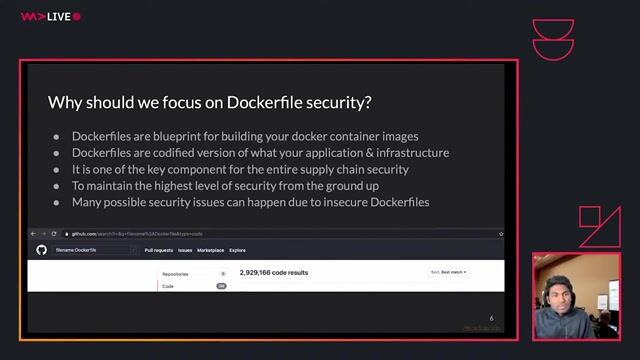
Why Dockerfile security is a critical foundation
A practical guide to writing secure Dockerfiles
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
02:28 MIN
Overcoming the challenges of container-based infrastructure
Building Reliable Serverless Applications with AWS CDK and Testing
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
Featured Partners
Related Videos
 42:45
42:45Kubernetes Security - Challenge and Opportunity
Marc Nimmerrichter
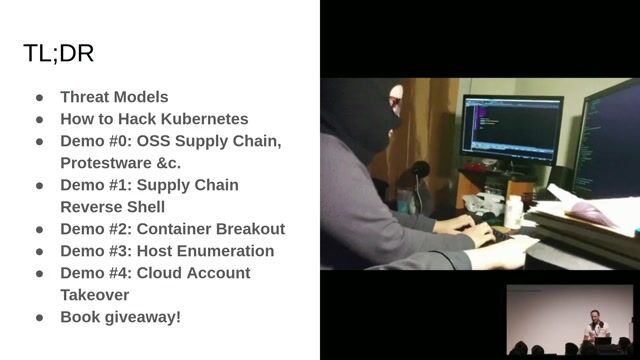 46:36
46:36Hacking Kubernetes: Live Demo Marathon
Andrew Martin
 42:25
42:25A practical guide to writing secure Dockerfiles
Madhu Akula
 30:33
30:33A solution to embed container technologies into automotive environments
Falk Langer & Lukas Stahlbock
 44:00
44:00Enhancing Workload Security in Kubernetes
Dimitrij Klesev & Andreas Zeissner
 32:55
32:55Open Source Secure Software Supply Chain in action
Natale Vinto
 40:00
40:00Local Development Techniques with Kubernetes
Rob Richardson
 23:08
23:08Kubernetes Security Best Practices
Rico Komenda
Related Articles
View all articles

.png?w=240&auto=compress,format)

From learning to earning
Jobs that call for the skills explored in this talk.

Mittwald CM Service GmbH & Co. KG
Espelkamp, Germany
Intermediate
Senior
Linux
Docker
DevOps
Kubernetes

smartclip Europe GmbH
Hamburg, Germany
Intermediate
Senior
GIT
Linux
Python
Kubernetes

Friedrich Kicherer GmbH & Co. KG
Ellwangen (Jagst), Germany
Junior
Intermediate
Senior
GIT
Docker
JavaScript


iits-consulting GmbH
München, Germany
Intermediate
Go
Docker
DevOps
Kubernetes


Aveniq AG
Senior
DevOps
Openshift
Terraform
Kubernetes
Microservices
+1

