Dimitrij Klesev & Andreas Zeissner
Enhancing Workload Security in Kubernetes
#1about 3 minutes
Understanding the Kubernetes securityContext for workloads
The securityContext field in a pod specification allows you to define privilege and access control settings for a pod or container.
#2about 4 minutes
Restricting kernel system calls with seccomp profiles
Seccomp profiles enhance security by allowing you to explicitly define which kernel system calls a containerized workload is permitted to make.
#3about 4 minutes
Hardening file system access with AppArmor profiles
AppArmor provides mandatory access control by defining profiles that restrict application capabilities like file reads, writes, and network access.
#4about 6 minutes
Implementing fine-grained control with SELinux contexts
SELinux uses a labeling system to enforce mandatory access control policies, providing granular control over process and object interactions.
#5about 2 minutes
Automating security with the Security Profiles Operator
The Security Profiles Operator simplifies the management and distribution of seccomp, AppArmor, and SELinux profiles across all nodes in a Kubernetes cluster.
#6about 5 minutes
Demo of blocking an in-memory execution attack
A live demonstration shows how a seccomp profile can block the `memfd_create` system call to prevent a fileless malware execution attack.
#7about 3 minutes
Demo of managing seccomp with the operator
This demo illustrates how the Security Profiles Operator uses a `ProfileBinding` to automatically apply a seccomp profile to workloads based on their image.
#8about 8 minutes
Demo of troubleshooting SELinux permissions
A practical demonstration shows how SELinux denies access by default and how to use audit logs and tools like `audit2allow` to diagnose and create new policies.
#9about 8 minutes
Q&A on AppArmor, fileless attacks, and eBPF
The speakers answer audience questions about applying AppArmor profiles, the nature of fileless malware, discovering system calls, and the role of eBPF.
Related jobs
Jobs that call for the skills explored in this talk.
Matching moments
02:52 MIN
Q&A on managed Kubernetes security in the cloud
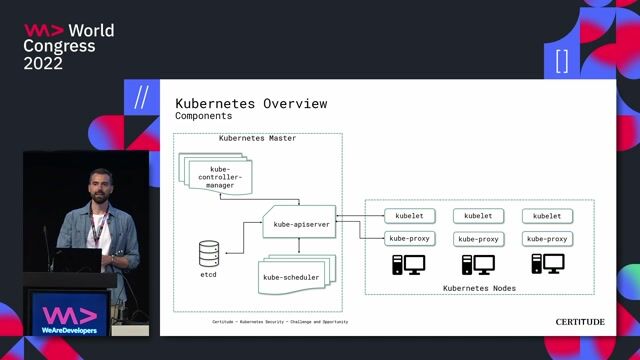
Kubernetes Security - Challenge and Opportunity
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
02:04 MIN
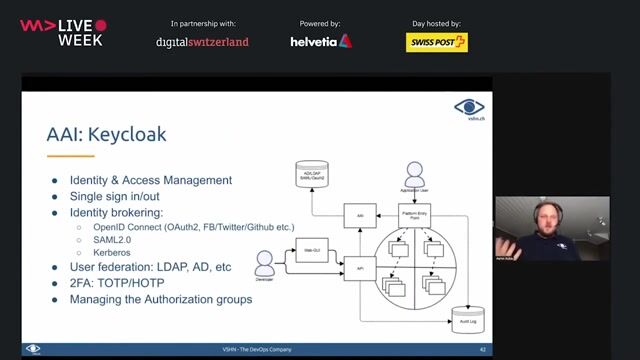
Centralizing security services in a Kubernetes ecosystem
DevSecOps: Security in DevOps
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
08:13 MIN
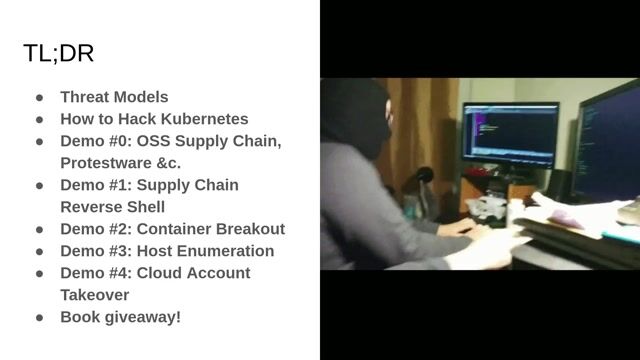
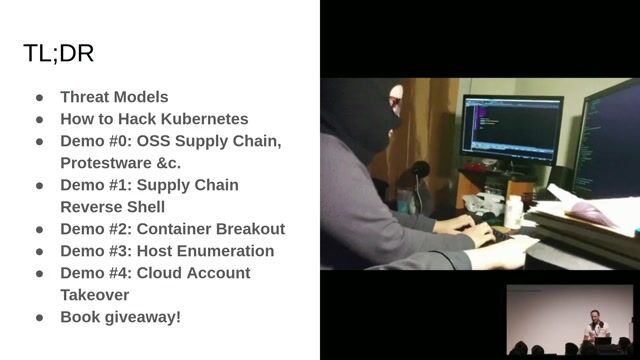
Understanding the Kubernetes threat landscape and adversaries
Hacking Kubernetes: Live Demo Marathon
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

01:27 MIN
The prevalence and impact of Kubernetes security incidents
Kubernetes Security Best Practices
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
04:28 MIN
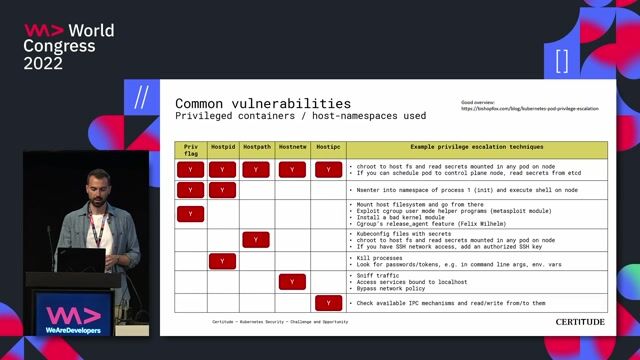
Identifying common Kubernetes security vulnerabilities
Kubernetes Security - Challenge and Opportunity
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
03:37 MIN
Addressing unique data protection challenges in Kubernetes
It's all about the Data
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
06:25 MIN
Security best practices for containers and Kubernetes
Microservices: how to get started with Spring Boot and Kubernetes
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

03:04 MIN
Moving from perimeter defense to workload microsegmentation
You can’t hack what you can’t see
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
Featured Partners
Related Videos
 42:45
42:45Kubernetes Security - Challenge and Opportunity
Marc Nimmerrichter
 46:36
46:36Hacking Kubernetes: Live Demo Marathon
Andrew Martin
 33:20
33:20DevSecOps: Security in DevOps
Aarno Aukia
 42:25
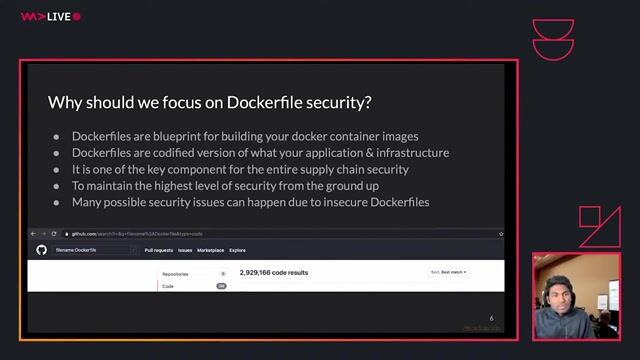
42:25A practical guide to writing secure Dockerfiles
Madhu Akula
 29:34
29:34You can’t hack what you can’t see
Reto Kaeser
 58:52
58:52Securing secrets in the GitOps Era
Davide Imola
 23:08
23:08Kubernetes Security Best Practices
Rico Komenda
 44:30
44:30Securing Your Web Application Pipeline From Intruders
Milecia McGregor
Related Articles
View all articles



From learning to earning
Jobs that call for the skills explored in this talk.

smartclip Europe GmbH
Hamburg, Germany
Intermediate
Senior
GIT
Linux
Python
Kubernetes

Mittwald CM Service GmbH & Co. KG
Espelkamp, Germany
Intermediate
Senior
Linux
Docker
DevOps
Kubernetes


Rocken AG
Linux
DevOps
Docker
Kubernetes
Load Balancing
+1




Rocken AG
Remote
CHF110-125K
Senior
DevOps
Openshift
Kubernetes
+1
