Ramona Schwering
Plants vs. Thieves: Automated Tests in the World of Web Security
#1about 3 minutes
Using Plants vs Zombies as a web security metaphor
The popular game Plants vs Zombies serves as an allegory for web security, where plants are countermeasures and zombies are threats to your application.
#2about 2 minutes
Why use existing test frameworks for security
Writing security tests with familiar frameworks like Cypress or Playwright can be a cost-effective alternative to buying specialized tools and allows you to leverage existing skills.
#3about 2 minutes
Understanding risks with the OWASP Top 10
The OWASP Top 10 list provides a critical starting point for security testing by ranking the most common web application security risks.
#4about 6 minutes
Writing end-to-end tests for injection attacks
A practical example demonstrates how to write a Cypress end-to-end test to detect an SQL injection vulnerability in a login form.
#5about 2 minutes
Testing for broken access control vulnerabilities
Negative tests can verify that users are correctly blocked from accessing protected pages, such as an administration panel, without proper permissions.
#6about 1 minute
How test frameworks can detect cryptographic failures
Modern testing frameworks like Cypress can inherently help detect cryptographic failures by erroring when an application attempts to navigate from an encrypted (HTTPS) to an unencrypted (HTTP) page.
#7about 2 minutes
Augmenting tests with specialized security tools
Since manual tests only cover known risks, integrating open-source tools and plugins can help discover unknown vulnerabilities and enhance your security posture.
#8about 2 minutes
Integrating security tests into your development pipeline
A five-step process for integrating security testing involves risk analysis, planning test layers, writing tests, executing them in pipelines, and iterating on the results.
#9about 2 minutes
Key takeaways for automated security testing
Test automation is a powerful complement to a security strategy, where even simple negative tests can significantly improve application safety when combined with tools and best practices.
Related jobs
Jobs that call for the skills explored in this talk.
Matching moments
04:47 MIN
Using automated tests as a line of defense
It's a (testing) trap! - Common testing pitfalls and how to solve them
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

04:11 MIN
Using automated tests as a web security defense
Plants vs. Thieves: Automated Tests in the World of Web Security
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

04:38 MIN
Hands-on security training for developers
How GitHub secures open source
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
09:34 MIN
Q&A on Web3 testing tools and security practices
Testing web3 applications
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

05:31 MIN
From vulnerability researcher to automated security founder
The transformative impact of GenAI for software development and its implications for cybersecurity
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

01:57 MIN
Using plugins and tools for unknown vulnerabilities
Plants vs. Thieves: Automated Tests in the World of Web Security
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

06:29 MIN
Writing end-to-end tests for injection vulnerabilities
Plants vs. Thieves: Automated Tests in the World of Web Security
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

01:24 MIN
Making web application security accessible to developers
What The Hack is Web App Sec?
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
Featured Partners
Related Videos
 24:09
24:09Plants vs. Thieves: Automated Tests in the World of Web Security
 24:19
24:19It's a (testing) trap! - Common testing pitfalls and how to solve them
Ramona Schwering
 25:38
25:38Measure and improve frontend performance by using test automation
Ramona Schwering
 45:24
45:24How will artificial intelligence change the future of software testing?
Evelyn Haslinger
 54:23
54:23Let's get visual - Visual testing in your project
Ramona Schwering
 44:40
44:40Enabling automated 1-click customer deployments with built-in quality and security
Christoph Ruggenthaler
 24:01
24:01What The Hack is Web App Sec?
Jackie
 2:08:06
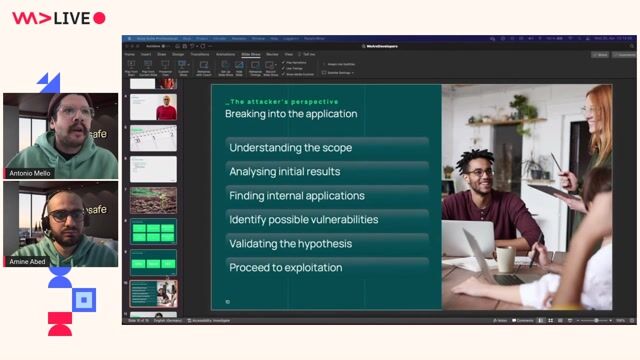
2:08:06The attacker's footprint
Antonio de Mello & Amine Abed
Related Articles
View all articles



From learning to earning
Jobs that call for the skills explored in this talk.


Vesterling Consulting GmbH
€70-90K
Software Architecture

GULP Information Services GmbH
Remote
Flutter
Routing
Continuous Integration


PVS eSolutions GmbH
JSON
DevOps
Gitlab
Grafana
Continuous Integration

PVS eSolutions GmbH
JSON
DevOps
Gitlab
Grafana
Continuous Integration



GULP Information Services GmbH