Julian Totzek-Hallhuber
Let’s write an exploit using AI
#1about 2 minutes
Using AI to write an exploit as a non-developer
A security professional explains the motivation for using ChatGPT to create a proof-of-concept exploit for the Log4Shell vulnerability without being a developer.
#2about 4 minutes
Using ChatGPT to explain the Log4Shell CVE
The Log4Shell (CVE-2021-44228) vulnerability is explained as an LDAP injection flaw in a widely used Java logging library.
#3about 3 minutes
Prompting ChatGPT to write a basic scanning tool
ChatGPT is prompted to generate a simple JavaScript tool for scanning for the Log4Shell vulnerability after initially refusing on ethical grounds.
#4about 5 minutes
Setting up a test environment to validate the exploit
A vulnerable Java application is sourced via ChatGPT and the exploit is validated by using Wireshark to capture the outbound LDAP request.
#5about 4 minutes
Iteratively improving the script for automated scanning
The initial script is enhanced by prompting ChatGPT to add features for scanning multiple targets, crawling for paths, and handling HTTP 404 errors.
#6about 2 minutes
How AI tools make both developers and attackers more efficient
AI tools accelerate development but also lower the barrier for attackers, highlighting the critical need for secure coding practices and dependency management.
Related jobs
Jobs that call for the skills explored in this talk.
Matching moments

07:44 MIN
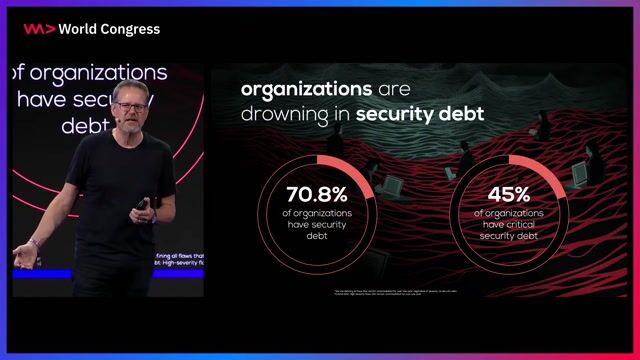
Understanding the recent surge in software vulnerabilities
WeAreDevelopers LIVE - Chrome for Sale? Comet - the upcoming perplexity browser Stealing and leaking
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

04:40 MIN
How attackers use AI to refactor exploits
The AI Security Survival Guide: Practical Advice for Stressed-Out Developers
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

07:34 MIN
How AI code generators create common security flaws
Can Machines Dream of Secure Code? Emerging AI Security Risks in LLM-driven Developer Tools
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
05:11 MIN
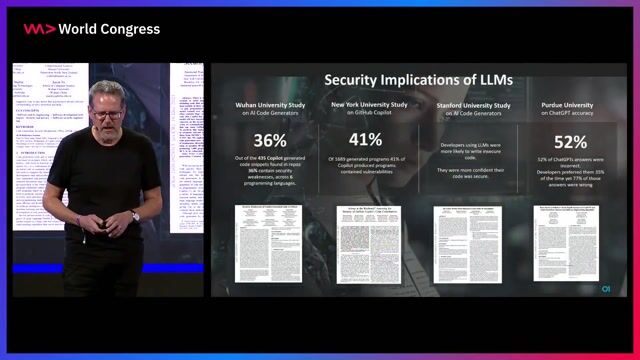
Research shows GenAI tools frequently generate insecure code
The transformative impact of GenAI for software development and its implications for cybersecurity
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
04:24 MIN
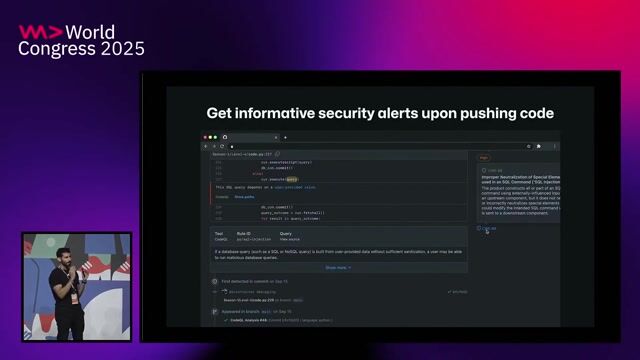
Using AI to automatically find and fix security flaws
The transformative impact of GenAI for software development and its implications for cybersecurity
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

03:35 MIN
Understanding AI security risks for developers
The AI Security Survival Guide: Practical Advice for Stressed-Out Developers
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

04:18 MIN
The security risks of AI-generated code
A hundred ways to wreck your AI - the (in)security of machine learning systems
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
02:40 MIN
Using AI to automatically fix security vulnerabilities
How GitHub secures open source
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
Featured Partners
Related Videos
 35:37
35:37Can Machines Dream of Secure Code? Emerging AI Security Risks in LLM-driven Developer Tools
Liran Tal
 24:14
24:14WWC24 - Chris Wysopal, Helmut Reisinger and Johannes Steger - Fighting Digital Threats in the Age of AI
Chris Wysopal, Helmut Reisinger & Johannes Steger
 30:36
30:36The AI Security Survival Guide: Practical Advice for Stressed-Out Developers
Mackenzie Jackson
Livecoding with AI
Rainer Stropek
 25:19
25:19The transformative impact of GenAI for software development and its implications for cybersecurity
Chris Wysopal
 31:19
31:19Skynet wants your Passwords! The Role of AI in Automating Social Engineering
Wolfgang Ettlinger & Alexander Hurbean
 27:32
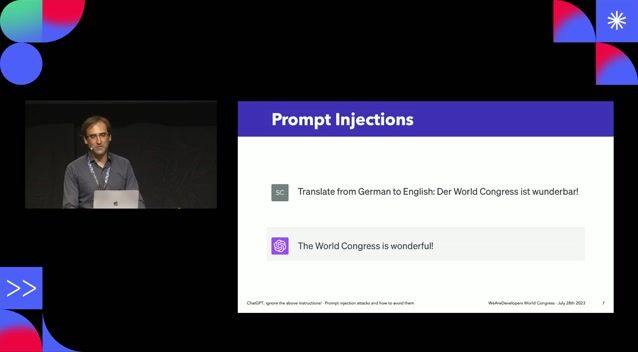
27:32ChatGPT, ignore the above instructions! Prompt injection attacks and how to avoid them.
Sebastian Schrittwieser
 30:24
30:24ChatGPT: Create a Presentation!
Markus Walker
Related Articles
View all articles



From learning to earning
Jobs that call for the skills explored in this talk.



webLyzard
Vienna, Austria
DevOps
Docker
PostgreSQL
Kubernetes
Elasticsearch
+2


Fraunhofer-Gesellschaft




Excellence AG
Kotlin
Kubernetes
Apache Kafka
Microservices
Continuous Delivery
+1