Wolfgang Ettlinger & Alexander Hurbean
Skynet wants your Passwords! The Role of AI in Automating Social Engineering
#1about 2 minutes
Understanding the dual role of AI in cybersecurity
Artificial intelligence can be used for both defensive security solutions and for malicious attacks like developing malware.
#2about 3 minutes
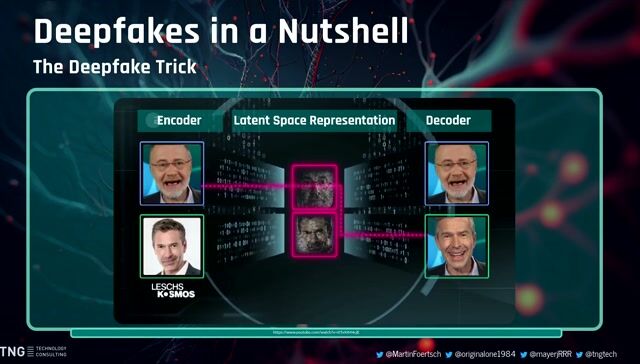
The threat of AI-generated deepfakes and voice cloning
Increasingly realistic AI-generated content, such as deepfakes and cloned voices, is being used for CEO fraud and fake kidnapping scams.
#3about 4 minutes
Automating social engineering with autonomous AI agents
Autonomous agents like AutoGPT can be programmed with a single goal to execute complex, multi-step social engineering attacks at scale.
#4about 5 minutes
A framework for automated phishing using LLMs
By jailbreaking models like ChatGPT, attackers can automate the creation of convincing phishing emails by feeding the model target information.
#5about 11 minutes
Building a proof-of-concept AI phishing email generator
A demonstration shows how a tool uses an LLM and service enumeration via DNS records to generate highly targeted phishing emails.
#6about 7 minutes
How to defend against AI-powered attacks
Defenses include user awareness, verification processes like S/MIME and PGP, adopting passkeys, and attempting prompt injection attacks on suspected bots.
Related jobs
Jobs that call for the skills explored in this talk.
Matching moments
03:11 MIN
Demonstrating deepfake attacks and social engineering
The AI Elections: How Technology Could Shape Public Sentiment
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

04:07 MIN
How AI accelerates and sophisticates cyber attacks
Tackling the Risks of AI - With AI
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

03:48 MIN
The perfection of social engineering with generative AI
WWC24 - Chris Wysopal, Helmut Reisinger and Johannes Steger - Fighting Digital Threats in the Age of AI
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

04:47 MIN
Protecting your online identity from AI-powered scams
WeAreDevelopers LIVE - Accessibility isn't magic, Longevity, Devrel in times of AI and more
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

04:40 MIN
How attackers use AI to refactor exploits
The AI Security Survival Guide: Practical Advice for Stressed-Out Developers
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

05:17 MIN
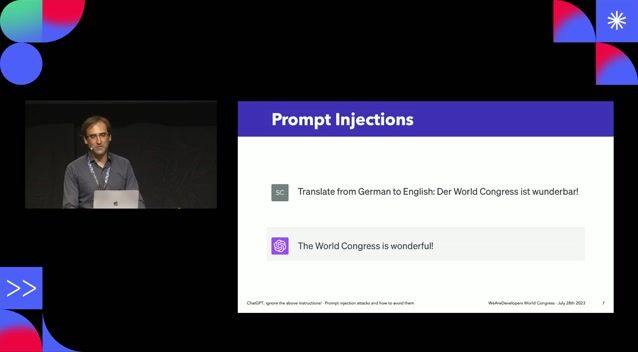
Manipulating AI with prompt injection and hidden commands
WeAreDevelopers LIVE - Is Software Ever Truly Accessible?
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

02:43 MIN
The evolving cybersecurity landscape with AI
Fireside Chat with Cloudflare's Chief Strategy Officer, Stephanie Cohen (with Mike Butcher MBE)
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

05:19 MIN
The rise of audio deepfakes in personal and corporate scams
Deep Fakes: The Lies We Can’t See
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
Featured Partners
Related Videos
 24:23
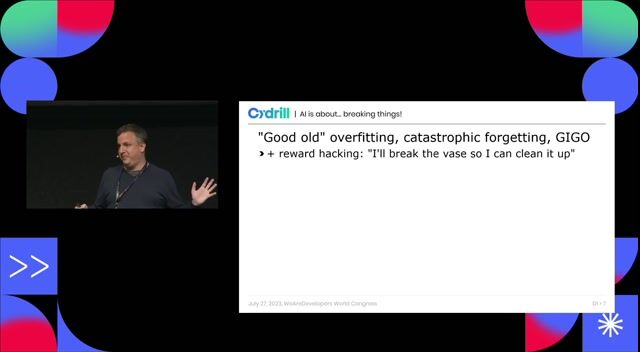
24:23A hundred ways to wreck your AI - the (in)security of machine learning systems
Balázs Kiss
 43:56
43:56Getting under the skin: The Social Engineering techniques
Mauro Verderosa
 27:32
27:32ChatGPT, ignore the above instructions! Prompt injection attacks and how to avoid them.
Sebastian Schrittwieser
 27:55
27:55Going Beyond Passwords: The Future of User Authentication
Gift Egwuenu
 24:49
24:49Deep Fakes: The Lies We Can’t See
George Proorocu
 24:14
24:14WWC24 - Chris Wysopal, Helmut Reisinger and Johannes Steger - Fighting Digital Threats in the Age of AI
Chris Wysopal, Helmut Reisinger & Johannes Steger
 27:02
27:02Hacking AI - how attackers impose their will on AI
Mirko Ross
 30:36
30:36The AI Security Survival Guide: Practical Advice for Stressed-Out Developers
Mackenzie Jackson
Related Articles
View all articles



From learning to earning
Jobs that call for the skills explored in this talk.


DTS Systeme GmbH
Docker
Kubernetes
Microservices
Machine Learning
Software Architecture

Virtual Identity AG





Deyan7 GmbH & Co. KG
