Moataz Nabil
DevSecOps: Injecting Security into Mobile CI/CD Pipelines
#1about 4 minutes
Why shift-left security is critical for mobile apps
The increasing speed of mobile releases makes traditional security a bottleneck, requiring a shift-left approach to find and fix bugs early in the development cycle.
#2about 4 minutes
Understanding the core principles of mobile DevOps
Mobile DevOps combines people, processes, and tools to enable continuous communication, integration, delivery, testing, and monitoring for mobile applications.
#3about 5 minutes
Integrating security into the DevOps lifecycle with DevSecOps
DevSecOps extends DevOps by making security a shared responsibility and integrating automated security checks throughout the entire development process.
#4about 5 minutes
Choosing the right security testing methods for your pipeline
Implementing DevSecOps involves choosing between static (SAST), dynamic (DAST), and interactive (IAST) security testing tools to automate vulnerability detection.
#5about 6 minutes
An example of a secure Android CI/CD workflow
A practical DevSecOps workflow for Android includes steps for static analysis, dependency scanning, dynamic testing, and vulnerability scanning at different stages.
#6about 5 minutes
Demo of building a DevSecOps pipeline with Bitrise
A live demonstration shows how to configure a mobile CI/CD pipeline in Bitrise with integrated steps for SonarQube, Firebase Test Lab, and Oversecured API.
#7about 1 minute
Key lessons learned from implementing DevSecOps
Implementing DevSecOps is a continuous journey that requires a cultural mindset shift, shared team responsibility, and a strong foundation in test automation.
#8about 15 minutes
Q&A on speed, team adoption, and common mistakes
The speaker answers audience questions about balancing speed with security, convincing management to adopt DevSecOps, and common security leaks in mobile development.
Related jobs
Jobs that call for the skills explored in this talk.
Matching moments
05:52 MIN
Integrating security into the DevOps lifecycle (DevSecOps)
Demystifying DevOps—Pros, cons, dos & don'ts
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

02:18 MIN
The evolution from traditional security to DevSecOps
DevSecOps culture
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

04:29 MIN
The modern DevSecOps approach to application security
Maturity assessment for technicians or how I learned to love OWASP SAMM
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

05:06 MIN
Hardening the CI/CD pipeline with automated security tools
You can’t hack what you can’t see
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in

02:41 MIN
Integrating security across the development lifecycle
Why Security-First Development Helps You Ship Better Software Faster
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
05:30 MIN
Integrating security tools into the developer workflow
Secure Code Superstars: Empowering Developers and Surpassing Security Challenges Together
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
04:43 MIN
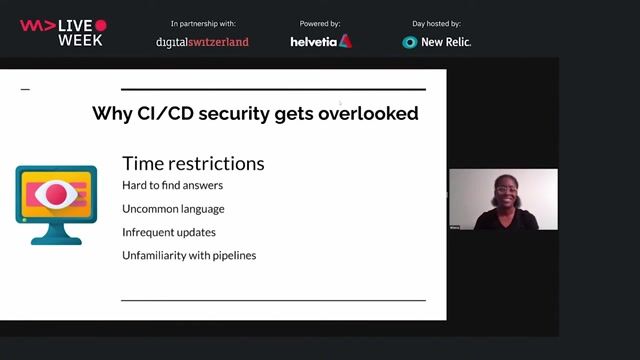
Why developers often overlook CI/CD security
Securing Your Web Application Pipeline From Intruders
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
04:40 MIN
Integrating security throughout the CI/CD process
Plan CI/CD on the Enterprise level!
Unlock Moments
Create a free account to watch a limited number of Moments each month.
Upgrade to PRO for unlimited access to the full archive.
Upgrade to PRO for unlimited access to the full archive.
You have an account? Log in
Featured Partners
Related Videos
 16:00
16:00DevSecOps culture
Ali Yazdani
 33:20
33:20DevSecOps: Security in DevOps
Aarno Aukia
 43:31
43:31Scalable architecture for mobile apps
Nachiket Apte
 44:30
44:30Securing Your Web Application Pipeline From Intruders
Milecia McGregor
 51:13
51:13Demystifying DevOps—Pros, cons, dos & don'ts
Thomas Fuchs, Waleed Arshad & Frank Dornberger & Idir Ouhab Meskine:
 26:50
26:50Organizational Change Through The Power Of Why - DevSecOps Enablement
Nazneen Rupawalla
 44:40
44:40Enabling automated 1-click customer deployments with built-in quality and security
Christoph Ruggenthaler
 34:44
34:44Applying DevOps in Flutter mobile development
Majid Hajian
Related Articles
View all articles



From learning to earning
Jobs that call for the skills explored in this talk.


GULP Information Services GmbH
Remote
Flutter
Routing
Continuous Integration




NTT DATA Deutschland GmbH
Remote
Node.js
Continuous Integration

NTT DATA Deutschland GmbH
Remote
Node.js
Continuous Integration

